1. Reviewing hosts in Foreman web UI
You can review hosts in the Foreman web UI to see them in one place and select the columns you need for daily work. When Enterprise Linux lifecycle data is available, check it in the same views to plan patches and track compliance.
1.1. Browsing hosts in Foreman web UI
In the Foreman web UI, you can browse all hosts recognized by Foreman, grouped by type.
The following host types are available when browsing hosts in the Foreman web UI:
-
All Hosts – a list of all hosts recognized by Foreman.
-
Discovered Hosts – a list of bare-metal hosts detected on the provisioning network by the Discovery plugin.
-
Host Collections – a list of user-defined collections of hosts used for bulk actions such as errata installation.
-
Search for a host: Type in the Search field, and use an asterisk (*) to perform a partial string search. For example, if searching for a host named
server.example.com, click the All Hosts page and typeserver*in the Search field. Alternatively,*ver*will also find the hostserver.example.com.WarningForeman server is listed as a host itself even if it is not self-registered. Do not delete Foreman server from the list of hosts.
-
Navigate between hosts: Click ⇄ next to the hostname. This displays a list of hosts in alphabetical order with a pagination arrow and a search bar to find the host you are looking for.
1.2. Selecting host columns
You can select what columns you want to see in the host table on the Hosts > All Hosts page.
|
Note
|
It is not possible to deselect the Name column. The Name column serves as a primary identification method of the host. |
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Manage columns.
-
Select columns that you want to display. You can select individual columns or column categories. Selecting or deselecting a category selects or deselects all columns in that category.
NoteSome columns are included in more than one category, but you can display a column of a specific type only once. By selecting or deselecting a specific column, you select or deselect all instances of that column.
-
You can now see the selected columns in the host table.
1.3. Lifecycle status of RHEL hosts
With Foreman, you can monitor the lifecycle status of your hosts by displaying upcoming End of Support (EOS) events. This is useful so that you can quickly identify which hosts require an update or action to maintain support.
Foreman provides multiple mechanisms to display information about upcoming EOS events for your Red Hat Enterprise Linux hosts:
-
Notification banner
-
A column on the Hosts index page
-
Alert on the Hosts index page for each host that runs Red Hat Enterprise Linux with an upcoming EOS event in a year as well as when support has ended
-
Ability to Search for hosts by EOS on the Hosts index page
-
Host status card on the host details page
For any hosts that are not running Red Hat Enterprise Linux, Foreman displays Unknown in the RHEL Lifecycle status and Last report columns.
When either the end of maintenance support or the end of extended lifecycle support approaches in a year, you will see a notification banner in the Foreman web UI if you have hosts with that Red Hat Enterprise Linux version. The notification provides information about the Red Hat Enterprise Linux version, the number of hosts running that version in your environment, the lifecycle support, and the expiration date. Along with other information, the Red Hat Enterprise Linux lifecycle column is visible in the notification.
1.4. Displaying RHEL lifecycle status
You can display the status of the end of support (EOS) for your Red Hat Enterprise Linux hosts in the table on the Hosts index page.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Manage columns.
-
Select the Content column to expand it.
-
Select RHEL Lifecycle status.
-
Click Save to generate a new column that displays the Red Hat Enterprise Linux lifecycle status.
-
Optional: You can use the Search field to search hosts by
rhel_lifecycle_status. It can have one of the following values:-
full_support -
maintenance_support -
approaching_end_of_maintenance -
extended_support -
approaching_end_of_support -
support_ended
-
1.5. Host global status overview
You can use the host global status in Foreman to see at a glance whether a host is OK, needs attention (Warning), or has errors. The status appears on the Hosts Overview page and helps you prioritize which hosts to investigate.
The host global status can have one of three possible values: OK, Warning, or Error. You can find global status on the Hosts Overview page. The status displays a small icon next to the host name and has a color that corresponds with the status. Hovering over the icon renders a tooltip with sub-status information to quickly find out more details. To view the global status for a host, in the Foreman web UI, navigate to Hosts > All Hosts.
- OK
-
No errors were reported by any sub-status. This status is highlighted with the color green.
- Warning
-
While no error was detected, some sub-status raised a warning. For example, there are no configuration management reports for the host even though the host is configured to send reports. It is a good practice to investigate any warnings to ensure that your deployment remains healthy. This status is highlighted with the color yellow.
- Error
-
Some sub-status reports a failure. For example, a run contains some failed resources. This status is highlighted with the color red.
If you want to search for hosts according to their status, use the syntax for searching in Foreman that is outlined in the Searching and Bookmarking in Administering Foreman, and then build your searches out by using the following status-related examples:
To search for hosts that have an OK status:
global_status = ok
To search for all hosts that deserve attention:
global_status = error or global_status = warning
1.6. Host sub-status overview
You can use host sub-statuses in Foreman to see the status of specific areas of a host, such as configuration, build, or content. Sub-statuses feed into the global host status and help you pinpoint what needs attention.
To view the sub-statuses of a host, in the Foreman web UI, navigate to Hosts > All Hosts and click on the host whose full status you want to inspect. You can view the global host status next to the name of the host and the host sub-statuses on the Host status card.
Each sub-status has its own set of possible values that are mapped to the three global status values. With any change of a sub-status, the global status is recalculated and the result is determined by the statuses of all sub-statuses.
The following sub-statuses are available in Foreman: There can be more sub-statuses depending on which plugins you add to your Foreman.
- Configuration
-
This sub-status is only relevant if Foreman uses a configuration management system like Ansible, Puppet, or Salt.
Possible values:
Label Global host status Alerts disabled
OK
Active
OK
Pending
OK
No changes
OK
No reports
OK / Warning
Out of sync
Warning
Error
Error
Additional information about the values of this sub-status:
-
Active: During the last configuration, some resources were applied.
-
Pending: During the last configuration, some resources would be applied but your configuration management integration was configured to run in
noopmode. -
No changes: During the last configuration, nothing changed.
-
No reports: This can be both a Warning or OK status. When there are no reports but the host uses an associated Smart Proxy for configuration management or the
always_show_configuration_statussetting is set totrue, it maps to Warning. Otherwise it maps to OK. -
Error: This indicates an error during configuration. For example, a configuration run failed to install a package.
-
Out of sync: A configuration report was not received within the expected interval, based on the
outofsync_intervalsetting. Reports are identified by an origin and can have different intervals based upon it.
-
- Build
-
This sub-status is only relevant for hosts provisioned from Foreman or hosts registered through global registration.
Possible values:
Label Global host status Number value Installed
OK
0
Pending installation
OK
1
Token expired
Error
2
Installation error
Error
3
- Compliance
-
Indicates if the host is compliant with OpenSCAP policies.
Possible values:
Label Global host status Number value Compliant
OK
0
Inconclusive
Warning
1
At least one incompliant
Error
2
- Execution
-
Status of the last completed remote execution job.
Possible values:
Label Global host status Number value Last execution succeeded / No execution finished yet
OK
0
Last execution failed
Error
1
Unknown execution status
OK
2 or 3
Last execution cancelled
OK
4
- Errata
-
Indicates if Errata is available on the host.
Possible values:
Label Global host status Number value Up to date
OK
0
Unknown
Warning
1
Needed errata
Error
2
Needed security errata
Error
3
- Traces
-
Indicates if the host needs a reboot or a process restart.
Possible values:
Label Global host status Number value Unknown
Warning
-1
Up to date
OK
0
Required process restart
Error
1
Required reboot
Error
2
If you want to search for hosts according to their sub-status, use the syntax for searching in Foreman that is outlined in the Searching and Bookmarking chapter of the Administering Foreman guide, and then build your searches out by using the following status-related examples:
You search for hosts' configuration sub-statuses based on their last reported state.
For example, to find hosts that have at least one pending resource:
status.pending > 0
To find hosts that restarted some service during last run:
status.restarted > 0
To find hosts that have an interesting last run that might indicate something has happened:
status.interesting = true
2. Managing host placement and associations
Hosts in Foreman define your infrastructure and are part of an organization and location to form logically structured groups. You can associate existing virtual machines to Foreman to actively manage them through Foreman.
2.1. Associating a virtual machine with Foreman from a hypervisor
Associate virtual machines (VMs) on a hypervisor with Foreman to manage them from a central location.
-
In the Foreman web UI, navigate to Infrastructure > Compute Resources.
-
Select a compute resource.
-
On the Virtual Machines tab, click Associate VMs to associate all VMs or select Associate VM from the Actions menu to associate a single VM.
2.2. Disassociating a VM from Foreman without removing it from a hypervisor
You can disassociate a virtual machine (VM) from Foreman if you no longer want to manage it. This does not delete the VM from its hypervisor.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the hosts that you want to disassociate.
-
From the options menu, select Disassociate hosts.
-
Click Disassociate.
2.3. Assigning a host to a specific organization
You can assign a host to a different organization so that the host is managed under the content, permissions, and settings of that organization.
|
Note
|
If your host is already registered with a different organization, you must first unregister the host before assigning it to a new organization.
To unregister the host, run |
-
Your user account has the
assign_organizationspermission. -
You belong to the organization that you want to assign to the host.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the checkbox of the host you want to change.
-
From the options menu, select Change associations > Organization. A new option window opens.
-
Select the organization that you want to assign your host to. Select Fix on mismatch.
NoteA mismatch happens if there is a resource associated with a host, such as a domain or subnet, and at the same time not associated with the organization you want to assign the host to. The option Fix on mismatch will add such a resource to the organization, and is therefore the recommended choice. The option Fail on mismatch will always result in an error message. For example, reassigning a host from one organization to another will fail, even if there is no actual mismatch in settings.
-
Click Change organization.
2.4. Assigning a host to a specific location
You can assign a host to a different location so that the host is managed under the subnets, domains, and settings of that location.
-
Your user account has the
assign_locationspermission. -
You belong to the location that you want to assign to the host.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the checkbox of the host you want to change.
-
From the options menu, select Change associations > Location. A new option window opens.
-
Select the location that you want for your host. Select the checkbox Fix on mismatch.
NoteA mismatch happens if there is a resource associated with a host, such as a domain or subnet, and at the same time not associated with the location you want to assign the host to. The option Fix on mismatch will add such a resource to the location, and is therefore the recommended choice. The option Fail on mismatch will always result in an error message. For example, reassigning a host from one location to another will fail, even if there is no actual mismatch in settings.
-
Click Change location.
2.5. Changing the content view environment of a host
You can change the content view environment of a host when you need to alter which content the host can consume from Foreman.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
On the Content view environment card, click the options icon and select Edit content view environments.
-
Select the environment.
-
Select the content view.
-
Click Save.
3. Managing host content settings and system purpose
You can set which content source and repositories a host uses and choose module streams for software versions. You can configure system purpose so subscription usage on the host reflects its role and usage.
3.1. Editing the system purpose of a host by using Foreman web UI
You can edit the system purpose attributes for your Red Hat Enterprise Linux host from the Foreman web UI. Setting system purpose defines the intended use of the system on your network and improves reporting accuracy in the Subscriptions service of the Red Hat Hybrid Cloud Console.
-
The host that you want to edit must be registered with the subscription-manager.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
On the Overview tab, click Edit on the System purpose card.
-
Select the system purpose attributes for your host.
-
Click Save.
3.2. Editing the system purpose of a host by using Hammer CLI
You can edit the system purpose attributes for your Red Hat Enterprise Linux host by using Hammer CLI. Setting system purpose defines the intended use of the system on your network and improves reporting accuracy in the Subscriptions service of the Red Hat Hybrid Cloud Console.
-
The host that you want to edit must be registered with the subscription-manager.
-
Log in to the host and edit the required system purpose attributes. For example, set the usage type to
Productionand the role toRed Hat Enterprise Linux Server. For the list of values, see Configuring System Purpose using the subscription-manager command-line tool in Automatically installing RHEL 8.# subscription-manager syspurpose set usage 'Production' # subscription-manager syspurpose set role 'Red Hat Enterprise Linux Server'
-
Verify the system purpose attributes for this host:
# subscription-manager syspurpose
3.3. Editing the system purpose of multiple hosts
You can edit the system purpose attributes of multiple Red Hat Enterprise Linux hosts at once from the Foreman web UI. Setting system purpose defines the intended use of the systems on your network and improves reporting accuracy in the Subscriptions service of the Red Hat Hybrid Cloud Console.
-
The hosts that you want to edit must be registered with the subscription-manager.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the Red Hat Enterprise Linux hosts that you want to edit.
-
Click the main menu icon and select Manage content > System purpose.
-
Select the system purpose attributes that you want to assign to the selected hosts. You can select one of the following values:
-
A specific attribute to set an all selected hosts.
-
No Change to keep the attribute set on the selected hosts.
-
(unset) to clear the attribute on the selected hosts.
-
-
Click Save.
3.4. Changing a module stream for a host
If you have a host running Enterprise Linux 8, you can modify the module stream for the repositories you install. You can enable, disable, install, update, and remove module streams from your host in the Foreman web UI.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Click the Content tab, then click the Module streams tab.
-
Click the vertical ellipsis next to the module and select the action you want to perform. You get a REX job notification once the remote execution job is complete.
3.5. Enabling custom repositories on hosts
You can enable custom repositories on a host from the Foreman web UI. This allows the host to install packages or consume other content from repositories you have added to Foreman.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select a host.
-
Select the Content tab, then select Repository sets.
-
From the dropdown, you can filter the Repository type column to Custom.
-
Select the desired number of repositories or click the Select All checkbox to select all repositories, then click the vertical ellipsis, and select Override to Enabled.
3.6. Changing the content source of a host
You can change the content source of a host so that the host consumes content from a different Smart Proxy. This helps you balance load or point the host to a closer or preferred content source.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Click the vertical ellipsis icon next to the Edit button and select Change content source.
-
Select Content Source, Lifecycle Content View, and Content Source from the lists.
-
Click Change content source.
NoteSome lifecycle environments can be unavailable for selection if they are not synced on the selected content source. For more information, see Adding lifecycle environments to Smart Proxy servers in Managing content.
-
You can complete the content source change by using remote execution or manually.
To update configuration on host using remote execution, click Run job invocation. For more information about running remote execution jobs, see Configuring and setting up remote jobs in Managing hosts.
To update the content source manually, execute the autogenerated commands from Change content source on the host.
4. Managing host records in Foreman
You can add a host record by cloning an existing host and choose whether Foreman manages it. You can remove the record from Foreman server when the system is decommissioned or re-registered elsewhere.
4.1. Cloning hosts in Foreman
You can clone an existing host in Foreman to create a new host with the same configuration, then change the name and network settings.
|
Note
|
Unlike cloning, creating a host is part of the host provisioning process. There are multiple provisioning methods and each requires different configuration of Foreman and Smart Proxies. For more information, see Provisioning hosts. |
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
In the Actions menu, click Clone.
-
On the Host tab, ensure to provide a Name different from the original host.
-
On the Interfaces tab, ensure to provide a different IP address.
-
Click Submit to clone the host.
4.2. Changing the managed status of a host
Hosts provisioned by Foreman are Managed by default. When a host is set to Managed, you can configure additional host parameters from Foreman server.
Additional host parameters that you can configure for your hosts are listed on the Operating System tab. If you change any settings on the Operating System tab, they will not take effect until you set the host to build and reboot it.
If you need to obtain reports about configuration management on systems using an operating system not supported by Foreman, set the host to Unmanaged.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Click Edit.
-
Click Manage host or Unmanage host to change the host’s status.
-
Click Submit.
4.3. Removing a host from Foreman by using Foreman web UI
You can remove a host from Foreman from the Foreman web UI when you decommission the host or no longer need to manage it. The host is permanently deleted from the Foreman database.
|
Warning
|
By default, deleting a host entry associated with a virtual machine does not destroy the virtual machine on the compute resource. To change the default behavior, navigate to Administer > Settings > Provisioning and set Destroy associated VM on host delete to Yes. |
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the hosts that you want to remove.
-
From the options menu, select Delete.
-
Select the checkbox I understand that this action cannot be undone.
-
Click Delete to remove the host from Foreman permanently.
4.4. Removing a host from Foreman by using Hammer CLI
You can remove a host from Foreman by using Hammer CLI when you decommission the host or no longer need to manage it. The host is permanently deleted from the Foreman database.
|
Warning
|
By default, deleting a host entry associated with a virtual machine does not destroy the virtual machine on the compute resource. To change the default behavior, navigate to Administer > Settings > Provisioning and set Destroy associated VM on host delete to Yes. |
-
Delete your host from Foreman:
$ hammer host delete \ --id My_Host_ID \ --location-id My_Location_ID \ --organization-id My_Organization_ID
Alternatively, you can use
--name My_Host_Nameinstead of--id My_Host_ID.
5. Managing host snapshots
You can install the Snapshot Management plugin and create virtual machine snapshots from Foreman to capture a point-in-time state before risky changes.
5.1. Installing the Snapshot Management plugin
You can install the Snapshot Management plugin on your Foreman.
-
Install the Snapshot Management plugin on your Foreman server:
# foreman-installer --enable-foreman-plugin-snapshot-management
5.2. Creating snapshots of a host
You can use the Snapshot Management plugin to create snapshots of hosts.
|
Caution
|
Keeping more than three snapshots per host slows down the creation and rollback process. Consider deleting older snapshots when creating new ones. |
-
You have installed the Snapshot Management plugin successfully. For more information, see Installing the Snapshot Management plugin.
-
Your host is running on VMware vSphere or Proxmox.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select a host.
-
In the Snapshots card, click Create Snapshot.
-
Enter a Name.
-
Optional: Enter a Description.
-
Optional: In the Snapshot Mode field, select Memory if you want to include the RAM in your snapshot or Quiesce if you want to ensure the full state of the VM is written to disk before creating the snapshot.
-
Click Submit to create a snapshot.
6. Working with host groups
To reduce repeated configuration when you manage many similar hosts, you can use host groups in Foreman as templates for shared host settings and apply them to many similar hosts. You can also nest host groups so child groups inherit from a parent and add specifics only where needed.
6.1. Host groups overview
You can use host groups in Foreman as templates for common host settings. Define the settings once and apply them to multiple hosts instead of configuring each host individually.
With host groups, you can define many settings for hosts, such as lifecycle environment, content view, or Ansible roles that are available to the hosts. Instead of defining the settings individually for each host, you can use host groups to define common settings once and apply them to multiple hosts.
You can create nested host groups.
|
Important
|
When you change the settings of an existing host group, the new settings do not propagate to the hosts assigned to the host group. Only Puppet class settings get updated on hosts after you change them in the host group. |
6.2. Nested host groups
You can create a hierarchy of host groups so that child host groups inherit and override settings from parent host groups.
Aim to have one base level host group that represents all hosts in your organization and provides general settings, and then nested groups that provide specific settings.
Foreman applies host settings in the following order when nesting host groups:
-
Host settings take priority over host group settings.
-
Nested host group settings take priority over parent host group settings.
You create a top-level host group named Base and two nested host groups named Webserver and Storage.
The nested host groups are associated with multiple hosts.
You also create host custom.example.com that is not associated with any host group.
You define the operating system on the top-level host group (Base) and Ansible roles on the nested host groups (Webservers and Storage).
| Top-level host group | Nested host group | Hosts | Settings inherited from host groups |
|---|---|---|---|
Base This host group applies the |
Webservers This host group applies the |
webserver1.example.com |
Hosts use the following settings:
|
webserver2.example.com |
|||
Storage This host group applies the |
storage1.example.com |
Hosts use the following settings:
|
|
storage2.example.com |
|||
[No host group] |
custom.example.com |
No settings inherited from host groups. |
|
You create a top-level host group named Base and two nested host groups named Webserver and Storage.
You also create host custom.example.com that is associated with the top-level host group Base, but no nested host group.
You define different values for the operating system and Ansible role settings on the top-level host group (Base) and nested host groups (Webserver and Storage).
| Top-level host group | Nested host group | Host | Settings inherited from host groups |
|---|---|---|---|
Base This host group applies these settings:
|
Webservers This host group applies these settings:
|
webserver1.example.com |
Hosts use the following settings:
|
webserver2.example.com |
|||
Storage This host group applies these settings:
|
storage1.example.com |
Hosts use the following settings:
|
|
storage2.example.com |
|||
[No nested host group] |
custom.example.com |
Host uses the following settings:
|
6.3. Creating a host group by using Foreman web UI
You can create a host group from the Foreman web UI to use as a template for common host settings.
-
In the Foreman web UI, navigate to Configure > Host Groups and click Create Host Group.
-
If you have an existing host group that you want to inherit attributes from, you can select a host group from the Parent list. If you do not, leave this field blank.
-
Enter a Name for the new host group.
-
Enter any further information that you want future hosts to inherit.
-
Click the Ansible Roles tab, and from the Ansible Roles list, select one or more roles that you want to add to the host. Use the arrow icon to manage the roles that you add or remove.
-
Click the additional tabs and add any details that you want to attribute to the host group.
NotePuppet fails to retrieve the Puppet CA certificate while registering a host with a host group associated with a Puppet environment created inside a
Productionenvironment.To create a suitable Puppet environment to be associated with a host group, manually create a directory:
# mkdir /etc/puppetlabs/code/environments/example_environment
-
Click Submit to save the host group.
6.4. Creating a host group by using Hammer CLI
You can create a host group by using Hammer CLI to use as a template for common host settings.
-
Create a host group:
$ hammer hostgroup create \ --architecture "My_Architecture" \ --content-source-id My_Content_Source_ID \ --content-view "My_Content_View" \ --domain "My_Domain" \ --lifecycle-environment "My_Lifecycle_Environment" \ --locations "My_Location" \ --medium-id My_Installation_Medium_ID \ --name "My_Host_Group" \ --operatingsystem "My_Operating_System" \ --organizations "My_Organization" \ --partition-table "My_Partition_Table" \ --puppet-ca-proxy-id My_Puppet_CA_Proxy_ID \ --puppet-environment "My_Puppet_Environment" \ --puppet-proxy-id My_Puppet_Proxy_ID \ --root-pass "My_Password" \ --subnet "My_Subnet"
6.5. Creating a host group for each lifecycle environment
You can create a host group for the Library lifecycle environment and nested host groups for other lifecycle environments. This organizes hosts by lifecycle stage, for example Development, Testing, and Production.
-
To create a host group for each lifecycle environment, run the following Bash script:
MAJOR="My_Major_Operating_System_Version" ARCH="My_Architecture" ORG="My_Organization" LOCATIONS="My_Location" PTABLE_NAME="My_Partition_Table" DOMAIN="My_Domain" hammer --output csv --no-headers lifecycle-environment list --organization "${ORG}" | cut -d ',' -f 2 | while read LC_ENV; do [[ ${LC_ENV} == "Library" ]] && continue hammer hostgroup create --name "rhel-${MAJOR}server-${ARCH}-${LC_ENV}" \ --architecture "${ARCH}" \ --partition-table "${PTABLE_NAME}" \ --domain "${DOMAIN}" \ --organizations "${ORG}" \ --query-organization "${ORG}" \ --locations "${LOCATIONS}" \ --lifecycle-environment "${LC_ENV}" done
6.6. Adding a host to a host group
You can add a host to a host group from the Foreman web UI so that the host inherits the settings of the host group.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Click Edit.
-
Select the host group from the Host Group list.
-
Click Submit.
-
The Details card under the Overview tab now shows the host group your host belongs to.
6.7. Changing the host group of a host
You can change the host group of a host so that the host inherits settings from the new host group.
|
Note
|
If you reprovision the host, the fresh values that the host group inherits from the new host group are applied. |
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Click Edit.
-
Select the new host group from the Host Group list.
-
Click Submit.
-
The Details card under the Overview tab now shows the host group your host belongs to.
7. Registering hosts to Foreman
Before you can use Foreman to manage hosts that have not been provisioned through Foreman, you must register them. You can register hosts through Foreman server or Smart Proxy server.
7.1. Supported clients in registration
Foreman supports the following operating systems and architectures for registration.
|
Note
|
The following combinations have been tested. Global registration is a provisioning template for a shell script, which can be extended for additional systems. If you decide to extend the template, please submit your changes to our repository. Thanks for your contribution! |
The hosts can use the following operating systems:
-
Amazon Linux
-
Debian
-
Enterprise Linux 10, 9, and 8
-
Fedora
-
OpenSUSE
-
SUSE Linux Enterprise Server
-
Ubuntu
The hosts can use the following architectures:
-
AMD and Intel 64-bit architectures
7.2. Registering hosts by using global registration
You can register hosts to Foreman by generating a curl or wget registration command on Foreman and running this command on multiple hosts.
Global registration uses two provisioning templates: Global Registration template and Linux host_init_config default template. That gives you complete control over the host registration process.
With this registration method, you can modify the initial configuration templates to enable additional features. For example, you can deploy Foreman SSH keys to hosts to enable remote execution jobs, configure hosts with Insights, or install the OpenVox agent on hosts to enable configuration management with Puppet.
If you use the Resource Quota plugin, registered hosts are automatically assigned to the Unassigned resource quota.
However, if you have the setting Resource Quota optional assignment set to No and no quotas to that a host can be assigned to, the host registration will fail because there is no valid quota the host can be assigned to.
For more information, see Limiting host resources in Administering Foreman.
You can extend registration options by plugins. For more information, see How to Create a Plugin and Slot and Fill.
7.2.1. Global parameters for registration
You can configure the following global parameters for registration.
You can view the parameters in the Foreman web UI by navigating to Configure > Global Parameters.
-
The
host_registration_insightsparameter is used in theinsightssnippet. If the parameter is set totrue, the registration installs and enables the Insights client on the host. If the parameter is set tofalse, Foreman prevents the installation and registration of the Insights client. The default value isfalse. When overriding the parameter value, set the parameter type toboolean. -
The
host_registration_insights_inventoryparameter controls Inventory uploads. If the parameter is set totrue, the host is included in the Insights Inventory report uploaded to the Red Hat Hybrid Cloud Console. If the parameter is set tofalse, the host is excluded from the Insights Inventory report upload. To upload inventory data without registering the host with the Insights client, set thehost_registration_insightsparameter tofalseand set thehost_registration_insights_inventorytotrue. -
The
host_packagesparameter is for installing packages on the host. -
The
host_registration_remote_executionparameter is used in theremote_execution_ssh_keyssnippet. If it is set totrue, the registration enables remote execution on the host. The default value istrue. -
The
remote_execution_ssh_keys,remote_execution_ssh_user,remote_execution_create_user, andremote_execution_effective_user_methodparameters are used in theremote_execution_ssh_keyssnippet. For more details, see the snippet.
You can navigate to snippets in the Foreman web UI through Hosts > Templates > Provisioning Templates.
7.2.2. Configuring a host for registration
Configure your host for registration to Foreman server or Smart Proxy server. You can use a configuration management tool to configure multiple hosts at once.
-
The host must be using a supported operating system. For more information, see Supported clients in registration.
-
The system clock on your Foreman server and any Smart Proxy servers must be synchronized across the network. If the system clock is not synchronized, SSL certificate verification might fail. For example, you can use the Chrony suite for timekeeping.
-
Enable and start a time-synchronization tool on your host. The host must be synchronized with the same NTP server as Foreman server and any Smart Proxy servers.
-
On Enterprise Linux:
# systemctl enable --now chronyd
-
-
Deploy the SSL CA file on your host so that the host can make a secured registration call.
-
Find where Foreman stores the SSL CA file by navigating to Administer > Settings > Authentication and locating the value of the SSL CA file setting.
-
Transfer the SSL CA file to your host securely, for example by using
scp. -
Login to your host by using SSH.
-
Copy the certificate to the truststore:
-
On Enterprise Linux:
# cp My_SSL_CA_file.pem /etc/pki/ca-trust/source/anchors
-
On Debian/Ubuntu:
# cp My_SSL_CA_file.pem /usr/local/share/ca-certificates/
-
-
Update the truststore:
-
On Enterprise Linux:
# update-ca-trust
-
On Debian/Ubuntu:
# update-ca-certificates
-
-
7.2.3. Registering a host by using Foreman web UI
You can register a host from the Foreman web UI with registration templates. This also enables you to set up various integration features and host tools during the registration process.
-
Your Foreman account has the Register hosts role assigned or a role with equivalent permissions.
-
Root privileges are available on the host that you want to register.
-
Either
curlorwgetis installed on the host that you want to register. -
Your host is configured for registration. For more information, see Configuring a host for registration.
-
An activation key must be available for your host. For more information, see Managing Activation Keys in Managing content.
-
Foreman Client repository for the operating system version of the host is synchronized on Foreman server and enabled in the activation key you use. For more information, see Adding content to Foreman in Managing content. This repository is required for the remote execution pull client, OpenVox agent, Tracer, and other tools.
-
If you want to use Smart Proxy servers instead of your Foreman server, ensure that you have configured your Smart Proxy servers accordingly.
ImportantIt is essential to add your Smart Proxy server to the list of trusted proxies on Foreman server!
For more information, see Configuring Smart Proxy for host registration and provisioning in Installing a Smart Proxy Server nightly on Enterprise Linux.
-
If your Foreman server or Smart Proxy server is behind an HTTP proxy, Subscription Manager on your host is configured to use the HTTP proxy for connection.
-
You have configured the operating system entry on Foreman for Enterprise Linux.
-
In the Foreman web UI, navigate to Hosts > Register Host.
-
Enter the details for how you want the registered host to be configured.
-
If you select a host group from the Host Group list, the following fields inherit their values from the host group:
-
Operating system
-
Activation Keys
-
Lifecycle environment
-
-
A Smart Proxy behind a load balancer takes precedence over the Smart Proxy selected in the Foreman web UI as the content source of the host.
-
-
On the General tab, in the Activation Keys field, enter one or more activation keys to assign to your host.
-
Specify any other registration details that you require. The available settings include the following:
-
On the General tab, in the Smart Proxy field, you can select the Smart Proxy to register your host through. A Smart Proxy behind a load balancer takes precedence over a Smart Proxy selected in the Foreman web UI as the content source of the host.
-
On the General tab, in the Download utility field, you can select
wgetif you want to register your host by using awgetcommand. By default, Foreman generates acurlcommand. -
On the General tab, you can select the Insecure option to make the first call insecure. During this first call, your host downloads the CA file from Foreman. Your host will use this CA file to connect to Foreman with all future calls making them secure.
Foreman community recommends that you avoid insecure calls.
If an attacker, located in the network between Foreman and your host, fetches the CA file from the first insecure call, the attacker will be able to access the content of the API calls to and from your host and the JSON Web Tokens (JWT). Therefore, if you have chosen to deploy SSH keys during registration, the attacker will be able to access your host using the SSH key.
-
On the Advanced tab, in the Repositories field, you can list repositories to be added before the registration is performed. You do not have to specify repositories if you provide them in an activation key.
-
On the Advanced tab, you can configure remote execution, Insights, and packages to be installed.
-
On the Advanced tab, in the Token lifetime (hours) field, you can change the validity duration of the JSON Web Token (JWT) that Foreman uses for authentication. The duration of this token defines how long the generated registration command works.
Note that Foreman applies the permissions of the user who generates the registration command to authorization of your host. If the user loses or gains additional permissions, the permissions of the JWT change too. Therefore, do not delete, block, or change permissions of the user during the token duration.
The scope of the JWTs is limited to the registration endpoints only and cannot be used anywhere else.
NoteForeman generates the registration command with parameters that search resources by ID. You can edit the registration command to search the following resources by title:
- Organization
-
URL fragment example:
organization=My%20Organizationororganization=My+Organization - Location
-
URL fragment example:
location=My%20Locationorlocation=My+Location - Host group
-
If a host group is nested, include the parent group separated with the slash character (
/).URL fragment example:
hostgroup=Parent%20Group%2FMy%20Host%20Group - Operating system
-
URL fragment example:
operatingsystem=My%20Operating%20Systemoroperatingsystem=My+Operating+System
The parameter values must be URL encoded.
-
On the Advanced tab, you can enable container and Flatpak registry access without a username or password by selecting the Set up container registry certs checkbox. Using certificate-based authentication also enforces lifecycle management of container and Flatpak content for the host.
-
-
Click Generate to generate a
curlcommand. -
Run the
curlcommand asrooton the host that you want to register. After registration completes, any Ansible roles assigned to a host group you specified when configuring the registration template will run on the host.
-
To set up monitoring of outdated services and applications using Tracer, see Configuring Tracer on a host in Managing hosts.
7.2.4. Registering a host by using Hammer CLI
You can register a host by using Hammer CLI with registration templates. This also enables you to set up various integration features and host tools during the registration process.
-
Your Foreman account has the Register hosts role assigned or a role with equivalent permissions.
-
Root privileges are available on the host that you want to register.
-
Either
curlorwgetis installed on the host that you want to register. -
Your host is configured for registration. For more information, see Configuring a host for registration.
-
An activation key must be available for your host. For more information, see Managing Activation Keys in Managing content.
-
Foreman Client repository for the operating system version of the host is synchronized on Foreman server and enabled in the activation key you use. For more information, see Adding content to Foreman in Managing content. This repository is required for the remote execution pull client, OpenVox agent, Tracer, and other tools.
-
If you want to use Smart Proxy servers instead of your Foreman server, ensure that you have configured your Smart Proxy servers accordingly.
ImportantIt is essential to add your Smart Proxy server to the list of trusted proxies on Foreman server!
For more information, see Configuring Smart Proxy for host registration and provisioning in Installing a Smart Proxy Server nightly on Enterprise Linux.
-
If your Foreman server or Smart Proxy server is behind an HTTP proxy, Subscription Manager on your host is configured to use the HTTP proxy for connection.
-
You have configured the operating system entry on Foreman for Enterprise Linux.
-
Use the
hammer host-registration generate-commandto generate the registration command to register your host. -
On your host that you want to register, run the registration command as
root.For more information, see the Hammer CLI help with
hammer host-registration generate-command --help.
-
To set up monitoring of outdated services and applications using Tracer, see Configuring Tracer on a host in Managing hosts.
7.2.5. Registering a host by using Foreman API
You can register a host by using Foreman API with registration templates. This also enables you to set up various integration features and host tools during the registration process.
-
Your Foreman account has the Register hosts role assigned or a role with equivalent permissions.
-
Root privileges are available on the host that you want to register.
-
Either
curlorwgetis installed on the host that you want to register. -
Your host is configured for registration. For more information, see Configuring a host for registration.
-
An activation key must be available for your host. For more information, see Managing Activation Keys in Managing content.
-
Foreman Client repository for the operating system version of the host is synchronized on Foreman server and enabled in the activation key you use. For more information, see Adding content to Foreman in Managing content. This repository is required for the remote execution pull client, OpenVox agent, Tracer, and other tools.
-
If you want to use Smart Proxy servers instead of your Foreman server, ensure that you have configured your Smart Proxy servers accordingly.
ImportantIt is essential to add your Smart Proxy server to the list of trusted proxies on Foreman server!
For more information, see Configuring Smart Proxy for host registration and provisioning in Installing a Smart Proxy Server nightly on Enterprise Linux.
-
If your Foreman server or Smart Proxy server is behind an HTTP proxy, Subscription Manager on your host is configured to use the HTTP proxy for connection.
-
You have configured the operating system entry on Foreman for Enterprise Linux.
-
Use the POST
/api/registration_commandsresource.
-
To set up monitoring of outdated services and applications using Tracer, see Configuring Tracer on a host in Managing hosts.
7.2.6. Registering a host by using Ansible
You can register a host with an Ansible playbook by using registration templates and set up various integration features and host tools during the registration process.
-
Use the
theforeman.foreman.registration_commandmodule.For more information, see the Ansible module documentation with
ansible-doc theforeman.foreman.registration_command.
7.2.7. Running custom code during host registration
You can customize the registration process by creating snippets with pre-defined names.
The Global Registration template includes these snippets automatically.
Therefore, you do not have to edit the template.
To add custom steps to registration, create one or both of the following snippets:
before_registration-
This snippet is loaded and executed by the
Global Registrationtemplate before registering your host to Foreman. after_registration-
This snippet is loaded and executed by the
Global Registrationtemplate after registering your host to Foreman.
Ensure you name the snippets precisely.
Otherwise, the Global Registration template cannot load them.
-
Your Foreman account has a role that grants the permissions
view_provisioning_templates,create_provisioning_templates,assign_organizations, andassign_locations. -
You have selected a particular organization and location context.
-
In the Foreman web UI, navigate to Hosts > Templates > Provisioning Templates.
-
Click Create Template.
-
In the Name field, enter the name of the required snippet:
before_registrationorafter_registration. -
In the template editor, create your snippet.
-
On the Type tab, select Snippet.
-
On the Locations tab, assign the snippet to required locations.
-
On the Organizations tab, assign the snippet to required organizations.
-
Click Submit.
7.2.8. Customizing the registration templates
You can customize the registration process by editing the provisioning templates.
Note that all default templates in Foreman are locked. If you want to customize the registration templates, you must clone the default templates and edit the clones.
The registration process uses the following provisioning templates:
-
The Global Registration template contains steps for registering hosts to Foreman. This template renders when hosts access the
/registerForeman API endpoint. -
The Linux host_init_config default template contains steps for initial configuration of hosts after they are registered.
-
Navigate to Hosts > Templates > Provisioning Templates.
-
Search for the template you want to edit.
-
In the row of the required template, click Clone.
-
Edit the template as needed. For more information, see Template writing reference.
-
Click Submit.
-
Navigate to Administer > Settings > Provisioning.
-
Change the following settings as needed:
-
Point the Default Global registration template setting to your custom global registration template,
-
Point the Default 'Host initial configuration' template setting to your custom initial configuration template.
-
7.2.9. Running Ansible roles during host registration
You can run Ansible roles when you are registering a host to Foreman.
-
Ansible integration is enabled on Foreman. For more information, see Enabling Ansible integration with Foreman in Configuring hosts by using Ansible.
-
The required Ansible roles have been imported from your Smart Proxy to Foreman. For more information, see Importing Ansible roles and variables in Configuring hosts by using Ansible.
-
Create a host group with Ansible roles. For more information, see Working with host groups.
-
Register the host by using the host group with assigned Ansible roles. For more information, see Registering a host by using Foreman web UI or Registering a host by using Hammer CLI.
7.3. Invalidating registration tokens
When you generate a registration command in global host registration, Foreman also generates a unique JSON Web Token (JWT) that is used to authorize the registration call from a host to Foreman server. If needed, you can invalidate a previously issued JWT.
A JWT is bound to the user that generated the registration command.
Users can configure a custom validity duration for the JWT. If the validity duration is too long or if the JWT has been compromised, the JWT poses a security concern. To mitigate this concern, the Foreman administrator or users with adequate permissions can invalidate existing JWTs.
You can also temporarily disable registration tokens by disabling a user. When you reenable the user, the user will be able to continue using their registration tokens.
7.3.1. Invalidating your own JWTs by using Foreman web UI
You can invalidate all registration JSON Web Tokens of the current user from the Foreman web UI.
-
In the Foreman web UI, click the user menu in the top bar and select My Account.
-
Select the Registration Tokens tab.
-
Click Invalidate JWTs.
-
In the confirmation window, click Confirm.
-
The Foreman web UI displays the following message:
Successfully invalidated registration tokens.
7.3.2. Invalidating your own JWTs by using Hammer CLI
You can invalidate all registration JSON Web Tokens of the current user by using Hammer CLI.
-
Invalidate all your registration tokens:
$ hammer user registration-token invalidate --user-id My_User_ID
7.3.3. Invalidating your own JWTs by using Foreman API
You can invalidate all registration JSON Web Tokens of the current user by using Foreman API.
-
Use the
DELETE /api/users/:user_id/registration_tokensresource.For more information, see the full API reference at
https://foreman.example.com/apidoc/v2.html.
7.3.4. Invalidating JWTs of other users by using Foreman web UI
You can invalidate all registration JSON Web Tokens of one or more users from the Foreman web UI.
-
Your Foreman user has a role that grants the
edit_userspermissions. For Foreman web UI, you also require theview_userspermission.
-
In the Foreman web UI, navigate to Administer > Users.
-
In the row of the user whose registration tokens you want to invalidate, from the actions menu, select Invalidate JWTs.
-
In the confirmation window, click Confirm.
-
The Foreman web UI displays the following message:
Successfully invalidated registration tokens for the user.
7.3.5. Invalidating JWTs of other users by using Hammer CLI
You can invalidate all registration JSON Web Tokens of one or more users by using Hammer CLI.
-
Your Foreman user has a role that grants the
edit_userspermissions. For Foreman web UI, you also require theview_userspermission.
-
Invalidate all registration tokens of a single user:
$ hammer user registration-token invalidate --user-id User_ID
-
Invalidate all registration tokens of multiple users:
$ hammer user registration-token invalidate-multiple --search "My_Search_Query"
7.3.6. Invalidating JWTs of other users by using API
You can invalidate all registration JSON Web Tokens of one or more users by using Foreman API.
-
Your Foreman user has a role that grants the
edit_userspermissions. For Foreman web UI, you also require theview_userspermission.
-
Invalidate all registration tokens of a single user by using the
DELETE /api/users/:user_id/registration_tokensresource. -
Invalidate all registration tokens of multiple users by using the
DELETE /api/registration_tokens?search=url-encoded-search-queryresource.
7.3.7. Invalidating JWTs of all users
You can invalidate all registration JSON Web Tokens of all users at once in the Foreman web UI.
-
Your Foreman user has a role that grants the
view_usersandedit_userspermissions.
-
In the Foreman web UI, navigate to Administer > Users.
-
Click Invalidate JWTs for all users.
-
In the confirmation window, click Confirm.
-
The Foreman web UI displays the following message:
Successfully invalidated registration tokens for all users.
8. Restarting applications on hosts through Tracer
If Tracer is available for your hosts, you can see which services need restarts after package updates and restart them when you choose.
8.1. Configuring Tracer on a host
You can install Tracer on hosts and access Traces on Foreman. Tracer displays a list of outdated services and applications that need to be restarted, as well as asks you to restart the host after, for example, a kernel update. Traces is the output generated by Tracer in the Foreman web UI.
-
The host is registered to Foreman.
-
Foreman Client repository for the operating system version of the host is synchronized on Foreman server, available in the content view and the lifecycle environment of the host, and enabled for the host. For more information, see Changing the repository sets status for a host in Foreman in Managing content.
-
Remote execution is enabled.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select your host.
-
On the Traces tab, click Enable Traces.
-
Select the provider to install
katello-host-tools-tracerfrom the list. -
Click Enable Tracer. You get a REX job notification after the remote execution job is complete.
-
If you get a list of applications that need to be restarted, select the ones that you want to restart.
-
Click Restart app, then click one of these buttons:
-
Restart via remote execution
-
Restart via customized remote execution
The first option restarts the application immediately, while the second one allows you to examine and customize the REX job.
-
8.2. Restarting applications on a host
You can restart applications on a host from the Foreman web UI when the host reports pending restarts, for example after package updates. Foreman uses remote execution to restart applications on the host.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
Select the Traces tab.
-
Select applications that you want to restart.
-
Select Restart via remote execution from the Restart app list. You will get a REX job notification once the remote execution job is complete.
9. Using SSL certificate for hosts
You can use SSL certificate on your hosts to enable encrypted communications between Foreman server, Smart Proxy server, and hosts. Before deploying it to your hosts, ensure that you have configured the SSL certificate to your Foreman server.
9.1. Deploying a SSL certificate to hosts
After you configure Foreman to use a SSL certificate, you must deploy the certificate to hosts registered to Foreman.
-
Update the SSL certificate on each host:
-
On Debian and Ubuntu:
# wget http://foreman.example.com/pub/katello-rhsm-consumer # chmod +x katello-rhsm-consumer # ./katello-rhsm-consumer
-
On Enterprise Linux 8+:
# dnf install http://foreman.example.com/pub/katello-ca-consumer-latest.noarch.rpm
-
On OpenSUSE and SUSE Linux Enterprise Server:
# zypper install http://foreman.example.com/pub/katello-ca-consumer-latest.noarch.rpm
-
10. Refreshing the self-signed CA certificate on hosts
When you change the CA certificate on your Foreman server, you must refresh the CA certificate on your hosts.
Ensure that you use a temporary dual CA certificate file for uninterrupted operation. For more information, see Planning for self-signed CA certificate renewal in Administering Foreman.
If you have already changed the CA certificate on Foreman server without using the temporary dual CA certificate file, you must refresh the certificate on hosts manually because the scripted variant will not recognize Foreman server.
|
Important
|
You only must redeploy the CA certificate if you use a self-signed CA certificate. |
10.1. Deploying the CA certificate on a host by using Script REX
You can use remote execution (REX) with the Script provider to deploy the CA certificate.
-
The host is registered to Foreman. :_mod-docs-content-type: SNIPPET
-
Remote execution is enabled on the host.
-
The CA certificate has been changed on Foreman server. For more information, see Planning for self-signed CA certificate renewal in Administering Foreman.
-
In the Foreman web UI, navigate to Monitor > Jobs.
-
Click Run Job.
-
From the Job category list, select Commands.
-
From the Job template list, select Download and run a script.
-
Click Next.
-
Select hosts on which you want to execute the job.
-
In the url field, enter the following URL:
https://foreman.example.com/unattended/public/foreman_ca_refresh
You can use HTTP when the CA certificate is expired.
-
Optional: Click Next and configure advanced fields and scheduling as you require.
-
Click Run on selected hosts.
-
If the host can access Foreman server, the following command succeeds on your host:
$ curl --head https://foreman.example.com
-
If the host can access Smart Proxy server, the following command succeeds on your host:
$ curl --head https://smartproxy.example.com:9090/features
Replace the port number with the port number you use.
10.2. Deploying the CA certificate on a host by using Ansible REX
You can use remote execution (REX) with the Ansible provider to deploy the CA certificate.
-
The host is registered to Foreman. :_mod-docs-content-type: SNIPPET
-
Remote execution is enabled on the host.
-
The CA certificate has been changed on Foreman server. For more information, see Planning for self-signed CA certificate renewal in Administering Foreman.
-
In the Foreman web UI, navigate to Monitor > Jobs.
-
Click Run Job.
-
From the Job category list, select Ansible Commands.
-
From the Job template list, select Download and execute a script.
-
Click Next.
-
Select hosts on which you want to execute the job.
-
In the url field, enter the following URL:
https://foreman.example.com/unattended/public/foreman_ca_refresh
You can use HTTP when the CA certificate is expired.
-
Optional: Click Next and configure advanced fields and scheduling as you require.
-
Click Run on selected hosts.
-
If the host can access Foreman server, the following command succeeds on your host:
$ curl --head https://foreman.example.com
-
If the host can access Smart Proxy server, the following command succeeds on your host:
$ curl --head https://smartproxy.example.com:9090/features
Replace the port number with the port number you use.
10.3. Deploying the CA certificate on a host manually
You can deploy the CA certificate on the host manually by rendering a public provisioning template, which provides the CA certificate.
-
You have root access on both your Foreman server and your host.
-
Download the certificate on your Foreman server:
# curl -o "foreman_ca_cert.crt" https://foreman.example.com/unattended/public/foreman_raw_ca
-
Transfer the CA certificate to your host securely, for example by using
scp. -
Login to your host by using SSH.
-
Copy the certificate to the Subscription Manager configuration directory:
# cp -u foreman_ca_cert.crt /etc/rhsm/ca/katello-server-ca.pem
-
Copy the certificate to the truststore:
-
On Enterprise Linux:
# cp foreman_ca_cert.crt /etc/pki/ca-trust/source/anchors
-
On Debian/Ubuntu:
# cp foreman_ca_cert.crt /usr/local/share/ca-certificates/
-
-
Update the truststore:
-
On Enterprise Linux:
# update-ca-trust
-
On Debian/Ubuntu:
# update-ca-certificates
-
-
If the host can access Foreman server, the following command succeeds on your host:
$ curl --head https://foreman.example.com
-
If the host can access Smart Proxy server, the following command succeeds on your host:
$ curl --head https://smartproxy.example.com:9090/features
Replace the port number with the port number you use.
11. Configuring network interfaces
Foreman supports specifying multiple network interfaces for a single host. This lets you add physical, virtual, bonded, bridge, or BMC interfaces as needed for your network layout.
11.1. Configuring a physical interface
You can configure a physical network interface for a host to set the MAC address, device identifier, and network or DNS settings.
-
Navigate to the Add Interface form:
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Edit next to the host you want to edit.
-
On the Interfaces tab, click Add Interface.
-
-
Specify the general interface settings:
-
Ensure Interface is selected as the type.
-
Specify a MAC address. This setting is required.
-
Specify the Device Identifier, for example
eth0.
-
-
Configure network and DNS settings:
-
Specify the DNS name associated with the host’s IP address.
-
Select a domain from the Domain list.
-
Select a subnet in the IPv4 Subnet or IPv6 Subnet list.
-
Specify the IPv4 address or IPv6 address.
NoteManaged interfaces with an assigned DHCP Smart Proxy server require this setting for creating a DHCP lease. DHCP-enabled managed interfaces are automatically provided with a suggested IP address.
-
-
Specify interface management options:
-
Select whether the interface is Managed.
-
Select whether this is the Primary interface for the host.
-
Select whether this is the Provision interface for the host.
-
Select whether to use the interface for Remote execution.
-
-
Click OK to save the interface configuration.
-
Click Submit to apply the changes to the host.
11.2. Configuring a virtual interface
You can configure a virtual interface for a host as a VLAN or an alias. Use a VLAN to connect to separate network segments on one physical interface, or use an alias to add another IP address to an existing interface.
-
A VLAN interface allows the host to connect to separate network segments using a single physical interface.
-
An alias interface is an additional IP address attached to an existing interface. An alias interface automatically inherits a MAC address from the interface it is attached to; therefore, you can create an alias without specifying a MAC address. The interface must be specified in a subnet with boot mode set to
static.
|
Note
|
Virtual interfaces currently require a MAC address of a physical device. Therefore, the configuration of these interfaces works only on bare-metal hosts. |
-
Navigate to the Add Interface form:
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Edit next to the host you want to edit.
-
On the Interfaces tab, click Add Interface.
-
-
Specify the general interface settings:
-
Ensure Interface is selected as the type.
-
If the virtual interface is managed, specify a MAC address.
-
Specify ID in the Device Identifier field.
-
For a VLAN, use the
eth1.10format. -
For an alias, use the
eth1:10format.
-
-
-
Configure a virtual NIC:
-
Select the Virtual NIC checkbox.
-
Optionally, specify a VLAN Tag.
-
Specify the identifier of the physical interface to which the virtual interface is Attached to, for example
eth1. This setting is required.
-
-
Click OK to save the interface configuration.
-
Click Submit to apply the changes to the host.
11.3. Configuring a bonded interface by using Foreman web UI
You can combine multiple physical interfaces by configuring a bonded interface for the host. Network interface card (NIC) bonding binds multiple interfaces into one logical interface that appears as a single device with one MAC address. Bonding increases bandwidth and provides redundancy by making two or more NICs act as one.
|
Note
|
Bonded interfaces currently require a MAC address of a physical device. Therefore, the configuration of these interfaces works only on bare-metal hosts. |
-
Navigate to the Add Interface form:
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Edit next to the host you want to edit.
-
On the Interfaces tab, click Add Interface.
-
-
Select Bond from the Type list.
-
Specify the general interface settings:
-
In the Device Identifier field, specify the interface ID in the
bond0format . -
Specify a MAC address.
-
If you are configuring a secondary interface, select Managed. Otherwise, Foreman does not apply the configuration.
-
-
Add the configuration specific to bonded interfaces:
-
Mode: Select the bonding mode.
-
Attached devices: Specify a comma-separated list of identifiers of attached devices. These can be physical interfaces or VLANs.
-
Bond options: Specify a space-separated list of configuration options, for example
miimon=100.
-
-
Click OK to save the interface configuration.
-
Click Submit to apply the changes to the host.
11.4. Configuring a bonded interface by using Hammer CLI
You can combine multiple physical interfaces by configuring a bonded interface for the host. Network interface card (NIC) bonding binds multiple interfaces into one logical interface that appears as a single device with one MAC address. Bonding increases bandwidth and provides redundancy by making two or more NICs act as one.
|
Note
|
Bonded interfaces currently require a MAC address of a physical device. Therefore, the configuration of these interfaces works only on bare-metal hosts. |
-
Create a host with a bonded interface:
$ hammer host create \ --ask-root-password yes \ --hostgroup My_Host_Group \ --ip=My_IP_Address \ --mac=My_MAC_Address \ --managed true \ --interface="identifier=My_NIC_1, mac=_My_MAC_Address_1, managed=true, type=Nic::Managed, domain_id=My_Domain_ID, subnet_id=My_Subnet_ID" \ --interface="identifier=My_NIC_2, mac=My_MAC_Address_2, managed=true, type=Nic::Managed, domain_id=My_Domain_ID, subnet_id=My_Subnet_ID" \ --interface="identifier=bondN, ip=My_IP_Address_2, type=Nic::Bond, mode=active-backup, attached_devices=[My_NIC_1,My_NIC_2], managed=true, domain_id=My_Domain_ID, subnet_id=My_Subnet_ID" \ --location "My_Location" \ --name "My_Host_Name" \ --organization "My_Organization" \ --subnet-id=My_Subnet_ID
Replace
bondNwithbondand the ID of your device identifier, for example,bond0.
11.5. Configuring a bridge interface
You can configure a bridge interface for a host to forward traffic between networks. Use a bridge when you need to connect network segments or run virtual machines with external network access.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click Edit next to the host you want to edit.
-
On the Interfaces tab, click Add Interface.
-
Select Bridge from the Type list.
-
Specify a MAC address.
-
In the Device Identifier field, specify the interface ID in the
bridge0format. -
If you are configuring a secondary interface, select Managed.
-
In the Attached devices field, specify a comma-separated list of identifiers of attached devices. These can be physical or virtual Ethernet devices, bonds, or VLAN devices.
-
Click OK to save the interface configuration.
-
Click Submit to apply the changes to the host.
11.6. Bonding modes available in Foreman
The following bonding modes are available when managing network interfaces in Foreman.
| Bonding Mode | Description |
|---|---|
balance-rr |
Transmissions are received and sent sequentially on each bonded interface. |
active-backup |
Transmissions are received and sent through the first available bonded interface. Another bonded interface is only used if the active bonded interface fails. |
balance-xor |
Transmissions are based on the selected hash policy. In this mode, traffic destined for specific peers is always sent over the same interface. |
broadcast |
All transmissions are sent on all bonded interfaces. |
802.a3 |
Creates aggregation groups that share the same settings. Transmits and receives on all interfaces in the active group. |
balance-tlb |
The outgoing traffic is distributed according to the current load on each bonded interface. |
balance-alb |
Receive load balancing is achieved through Address Resolution Protocol (ARP) negotiation. |
11.7. Configuring a baseboard management controller (BMC) interface
You can configure a baseboard management controller (BMC) interface for a host. A BMC lets you remotely monitor and manage the physical state of the machine and control host power from Foreman. This applies to bare-metal hosts that support BMC.
-
Power management is enabled on Foreman server. For more information, see Enabling power management on hosts in Installing Foreman Server with Katello nightly plugin on Enterprise Linux.
-
If you use Smart Proxy server instead of Foreman server, power management must be enabled on your Smart Proxy server. For more information, see Enabling power management on hosts in Installing a Smart Proxy Server nightly on Enterprise Linux.
-
You know the MAC address, IP address, and other details of the BMC interface on the host, and authentication credentials for that interface.
NoteYou only need the MAC address for the BMC interface if the BMC interface is managed, so that it can create a DHCP reservation.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Edit your host.
-
On the Interfaces tab, click Add Interface.
-
Select BMC from the Type list.
-
Specify the general interface settings:
-
If the BMC is managed, specify a MAC address.
-
Specify the Device Identifier.
-
-
Specify the configuration options specific to BMC interfaces:
-
Username and Password: Specify any authentication credentials required by BMC.
-
Provider: Specify the BMC provider.
-
-
Click OK to save the interface configuration.
-
Click Submit to apply the changes to the host.
11.8. Network interface configuration options
When adding a network interface, you need to specify several configuration options. The following lists provide information on the relevant options for the different types of interfaces.
- Physical interface settings
-
- Device Identifier
-
The identifier is used to specify this physical interface when creating bonded interfaces, VLANs, and aliases.
- DNS name
-
Foreman saves this name in the Smart Proxy server associated with the selected domain (the "DNS A" field) and Smart Proxy server associated with the selected subnet (the "DNS PTR" field). A single host can therefore have several DNS entries.
- Domain
-
Specifies the domain associated with the network interface. To create and manage domains, navigate to Infrastructure > Domains.
- Subnet
-
Specifies the subnet associated with the network interface. To create and manage subnets, navigate to Infrastructure > Subnets.
- Managed interface
-
If the interface is managed, configuration is pulled from the associated Smart Proxy server during provisioning, and DNS and DHCP entries are created. If you use provisioning with installer automation, a configuration file is automatically created for the interface.
NoteAdditional interfaces have the Managed flag enabled by default, which means the new interface is configured automatically during provisioning by the DNS and DHCP Smart Proxy servers associated with the selected subnet. This requires a subnet with correctly configured DNS and DHCP Smart Proxy servers. If you use a Kickstart method for host provisioning, configuration files are automatically created for managed interfaces in the post-installation phase at
/etc/sysconfig/network-scripts/ifcfg-interface_id. - Primary interface
-
The DNS name from the primary interface is used as the host portion of the FQDN.
- Provision
-
Network boot uses the provisioning interface. For image-based provisioning, the script to complete the provisioning is executed through the provisioning interface.
- Virtual interface settings
-
- Tag
-
You can set a VLAN tag to trunk a network segment from the physical network through to the virtual interface.
-
If you do not specify a tag, managed interfaces inherit the VLAN tag of the associated subnet.
-
User-specified entries from this field are not applied to alias interfaces.
-
- Bonded interface settings
-
- Mode
-
The bonding mode defines a policy for fault tolerance and load balancing. See Bonding modes available in Foreman for a brief description of each bonding mode.
12. Upgrading hosts to next major Enterprise Linux release
You can use a job template to upgrade your Enterprise Linux hosts to the next major release. This helps you keep hosts on a supported release and can be run across multiple hosts by using remote execution.
Foreman community supports the following upgrade paths:
-
Enterprise Linux 7 to Enterprise Linux 8
-
Enterprise Linux 8 to Enterprise Linux 9
-
Enterprise Linux 9 to Enterprise Linux 10
-
Your Enterprise Linux hosts meet the requirements for the upgrade.
-
For Enterprise Linux 7 to Enterprise Linux 8 upgrade, see Planning an upgrade in Upgrading from RHEL 7 to RHEL 8.
-
For Enterprise Linux 8 to Enterprise Linux 9 upgrade, see Planning an upgrade to RHEL 9 in Upgrading from RHEL 8 to RHEL 9.
-
For Enterprise Linux 9 to Enterprise Linux 10 upgrade, see Planning an upgrade to RHEL 10 in Upgrading from RHEL 9 to RHEL 10.
-
-
Your Enterprise Linux hosts are prepared for the upgrade.
-
For Enterprise Linux 7 to Enterprise Linux 8 upgrade, see Preparing a RHEL 7 system for the upgrade in Upgrading from RHEL 7 to RHEL 8.
-
For Enterprise Linux 8 to Enterprise Linux 9 upgrade, see Preparing a RHEL 8 system for the upgrade in Upgrading from RHEL 8 to RHEL 9.
-
For Enterprise Linux 9 to Enterprise Linux 10 upgrade, see Preparing a RHEL 9 system for the upgrade in Upgrading from RHEL 9 to RHEL 10.
-
-
Remote execution is enabled on Foreman. For more information, see Configuring and setting up remote jobs.
-
Foreman SSH keys are distributed to the hosts that you want to upgrade. For more information, see Distributing SSH keys for remote execution.
-
On Foreman, enable the Leapp plugin:
# foreman-installer --enable-foreman-plugin-leapp
-
Optional: Customize the upgrade by modifying the default pre-upgrade check and upgrade job templates.
-
Clone and modify the Run preupgrade via Leapp template, the Run upgrade via Leapp template, or both. For more information, see Customizing job templates.
-
In the Foreman web UI, navigate to Administer > Remote Execution Features.
-
If you modified the pre-upgrade template, click leapp_preupgrade. If you modified the upgrade template, click leapp_upgrade.
-
In the Job Template drop-down menu, select your template.
-
Click Submit. The leap_preupgrade and leapp_upgrade remote execution features now point to the modified templates.
-
-
Run a pre-upgrade check:
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the hosts that you want to upgrade.
-
If you want to upgrade to the latest available release, expand the Schedule a Job drop-down menu and select Preupgrade check with Leapp.
-
If you want to upgrade to a specific release version, click Schedule a job. From the Job category list, select Leapp - Preupgrade. Follow the job wizard to start the preupgrade check.
-
-
Review the results of the pre-upgrade check:
NoteThe results of the pre-upgrade check are only available in the legacy Foreman web UI job invocation details page.
-
Navigate to Monitor > Jobs. Click the pre-upgrade check job.
-
From the Rerun all dropdown menu, click Legacy UI.
-
Click the Leapp preupgrade report tab to see if Leapp has found any issues on your hosts. Issues that have the Inhibitor flag are considered crucial and are likely to break the upgrade procedure. Issues that have the Has Remediation flag contain remediation that can help you fix the issue.
-
Click an issue that is flagged as Has Remediation to expand it.
-
If the issue contains a remediation Command, you can fix it directly from Foreman using remote execution. Select the issue.
-
If the issue contains only a remediation Hint, use the hint to fix the issue on the host manually.
Repeat this step for other issues.
-
-
After you selected any issues with remediation commands, click Fix Selected and submit the job.
-
After the issues are fixed, click Rerun, and then click Submit to run the pre-upgrade check again to verify that the hosts you are upgrading do not have any issues and are ready to be upgraded.
-
-
Start the upgrade:
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the hosts that you want to upgrade.
-
If you want to upgrade to the latest available release version, expand the Schedule a Job drop-down menu and select Upgrade with Leapp.
-
If you want to upgrade to a specific release version, click Schedule a job. From the Job category list, select Leapp - Upgrade. Follow the job wizard to start the upgrade.
-
13. Converting hosts to Red Hat Enterprise Linux
You can convert Red Hat Enterprise Linux derivative distributions, such as CentOS or Oracle Linux, to supported Red Hat Enterprise Linux on a host while retaining installed applications and configurations. This helps you move your hosts to Red Hat Enterprise Linux without a full reinstall.
13.1. Overview of the conversion process
You can use the Convert2RHEL utilities in Foreman to convert CentOS or Oracle Linux hosts to Red Hat Enterprise Linux. The process replaces packages with Red Hat Enterprise Linux equivalents while retaining applications and configurations.
The conversion process is similar to a minor release upgrade of Red Hat Enterprise Linux in which every RPM package on the system is replaced. Third-party packages and non-Red Hat packages that are not available in Red Hat Enterprise Linux are retained.
The Convert2RHEL utility removes unnecessary packages such as logos or packages known to cause issues during the conversion.
The utility replaces the CentOS-release or Oracle-release package with the rhel-release package, and all packages signed by CentOS or Oracle with their Red Hat equivalents.
The utility also subscribes the host to Red Hat Subscription Management.
The duration of the conversion process depends on the number of packages that have to be replaced, network speed, storage speed, and similar factors.
These following conversions are supported by Foreman community:
-
CentOS Linux 7 to Red Hat Enterprise Linux 7
-
Oracle Linux 7 to Red Hat Enterprise Linux 7
-
Oracle Linux 8 to Red Hat Enterprise Linux 8
You can use the Ansible Playbook for other conversions as well, but in those cases you must enable required repositories and configure activation keys manually instead of using the Ansible role and variables. However, this approach was not tested and is not supported.
If you convert to a RHEL version that is in the Extended Life Phase and you do not plan to upgrade your host to a fully supported RHEL version, Red Hat recommends using an Extended Life Cycle Support (ELS) Add-On subscription during the conversion. Note that the conversion and the subsequent upgrade without an ELS subscription come with a limited support scope.
13.2. Converting a host to Red Hat Enterprise Linux
You can convert a host to Red Hat Enterprise Linux by using the Convert2RHEL Ansible role and playbook in Foreman. The role prepares conversion data on Foreman server, and the playbook runs the conversion on the host.
-
You have reviewed the supported conversion paths in Red Hat Enterprise Linux 8 Converting from a Linux distribution to RHEL using the Convert2RHEL utility.
-
A subscription manifest is uploaded to your Foreman with sufficient Red Hat Enterprise Linux entitlements allocated for the conversions you intend. Alternatively, you can use Ansible variables to tell the role to import the manifest from disk. The manifest must be imported to the organization to which you will register hosts for conversion.
You can update your allocations and download the updated manifest from the Red Hat Customer Portal. For more information, see Exporting and downloading a manifest in Creating and managing manifests for a connected Satellite Server.
-
Red Hat repositories are enabled and synchronized in Foreman for the minor Red Hat Enterprise Linux version to which you convert your hosts. For more information, see Enabling Red Hat Repositories and Synchronizing repositories on demand in Managing content.
-
Import the
theforeman.foreman.convert2rhelAnsible role and variables. For more information, see Importing Ansible Roles and Variables in Configuring hosts by using Ansible. -
Configure Ansible variables for generation of conversion data. For more information, see Ansible variables for conversion.
-
Assign the
theforeman.foreman.convert2rhelrole to the host that represents Foreman server. For more information, see Assigning Ansible Roles to an Existing Host in Configuring hosts by using Ansible. -
Run the Ansible role on Foreman server. For more information, see Running Ansible Roles on a Host in Configuring hosts by using Ansible.
The Ansible role generates data required for host conversion, that is, repositories, certificates, activation keys, and host groups. The role enables the
rhel-7-server-rpmsrepository with the 7Server release and x86_64 architecture, orrhel-8-for-x86_64-baseos-rpmsandrhel-8-for-x86_64-appstream-rpms, or both, depending on which variables you have set in the previous steps. -
Register a host for conversion by using a generated host group.
Use the global registration template to register and subscribe your host before the conversion. Select the host group that was generated for the conversion you intend, such as
CentOS 7 convertingif you convert the host from CentOS 7. For more information, see Registering hosts by using global registration. -
Run the pre-conversion analysis on the host group to verify if your hosts are ready for the conversion. Execute a remote job with the following settings:
-
Job category:
Convert 2 RHEL -
Job template:
Convert2RHEL analyze -
If you want to use an Extended Lifecycle Support add-on subscription, set the ELS option to
yes.For more information, see Configuring and setting up remote jobs.
Review pre-conversion analysis reports and resolve all issues that are blocking the conversion. Repeat this step until you resolve all blocking issues. For more information, see Reviewing the pre-conversion analysis report in Red Hat Enterprise Linux 8 Converting from a Linux distribution to RHEL using the Convert2RHEL utility.
-
-
Run the Convert2RHEL playbook on the host group. Execute a remote job with the following settings:
-
Job category:
Convert 2 RHEL -
Job template:
Convert to RHEL -
Activation key:
-
convert2rhel_rhel7if you convert to Red Hat Enterprise Linux 7 -
convert2rhel_rhel8if you convert to Red Hat Enterprise Linux 8
-
-
If you want to use an Extended Lifecycle Support add-on subscription, set the ELS option to
yes.
For more information, see Configuring and setting up remote jobs.
-
13.3. Ansible variables for conversion
Configure the required Ansible variables for the Convert2RHEL role before you run it to generate conversion data on Foreman server. This reference lists the variables and their intended values.
Foreman imports most of the required Ansible variables from the theforeman.foreman.convert2rhel role.
However, some variables are not imported.
These variables are marked with an asterisk * in the tables below.
You must create those additional variables manually and assign them to the theforeman.foreman.convert2rhel role.
| Name | Type | Intent and value |
|---|---|---|
|
string |
URL of your Foreman server, such as |
|
string |
Your user name |
|
string |
Your password |
|
string |
Name of your organization |
|
boolean |
Set to |
|
boolean |
Set to |
|
boolean |
Set to |
|
boolean |
Enables Red Hat Enterprise Linux 7 repositories.
Set to |
|
boolean |
Set to |
|
boolean |
Enables Red Hat Enterprise Linux 8 repositories.
Set to |
|
boolean |
Set to |
| Name | Type | Intent and value |
|---|---|---|
|
string |
Path to a manifest to upload from disk, such as |
|
string |
Minor release version, such as |
14. Host management and monitoring by using Cockpit
You can use the Cockpit web interface to perform actions and monitor Enterprise Linux hosts. Enable Cockpit integration in Foreman to view host dashboards and use Cockpit features, such as Lorax Composer, from within the Foreman web UI.
14.1. Enabling Cockpit on Foreman
You can enable Cockpit on Foreman server so that you can access Cockpit features for your hosts from within the Foreman web UI.
-
You have root or sudo access on Foreman server.
-
Enable Cockpit on your Foreman server:
# foreman-installer --enable-foreman-plugin-remote-execution-cockpit --reset-foreman-plugin-remote-execution-cockpit-ensure
14.2. Managing and monitoring hosts using Cockpit
You can access the Cockpit UI through the Foreman web UI to manage and monitor Enterprise Linux hosts. Use it to view dashboards, run commands, or use integrated features such as Lorax Composer.
-
You have enabled Cockpit in Foreman.
-
You have installed Cockpit on the host that you want to manage and monitor.
Foreman provides a job template named Service Action – Enable Web Console under the Ansible Services job category that you can use to install Cockpit. For more information about running remote jobs, see Configuring and setting up remote jobs.
-
Foreman or Smart Proxy can authenticate to the host with SSH keys. For more information, see Distributing SSH keys for remote execution.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select the host that you want to manage and monitor with Cockpit.
-
In the upper right of the host window, click the vertical ellipsis and select Web Console.
You can now access the full range of features available for host monitoring and management, for example, Lorax Composer, through Cockpit.
14.3. Disabling Cockpit on Foreman
You can disable Cockpit on Foreman server when you no longer need to access Cockpit features for hosts from the Foreman web UI.
-
Disable Cockpit on your Foreman server:
# foreman-installer --foreman-plugin-remote-execution-cockpit-ensure absent
ImportantYou can enable or disable Cockpit integration independently on Smart Proxy servers. After completing the procedure on your Foreman server, you can disable Cockpit integration on your Smart Proxy servers:
# foreman-installer --foreman-proxy-plugin-remote-execution-script-cockpit-integration false
15. Monitoring hosts by using Insights in Red Hat Hybrid Cloud Console
You can use the Insights advisor service in the Red Hat Hybrid Cloud Console to assess system health on hosts running Red Hat Enterprise Linux. You can use the Insights dashboard in the Red Hat Hybrid Cloud Console to quickly analyze recommendations for remediation, vulnerabilities, and more.
15.1. Insights in Red Hat Hybrid Cloud Console overview
When you use Insights in the Red Hat Hybrid Cloud Console, the Insights client on your hosts collects data and Foreman forwards it to the cloud for analysis.
If you use Insights in the Red Hat Hybrid Cloud Console:
-
You can use Insights services online in the Red Hat Hybrid Cloud Console.
-
The Insights client collects data of your hosts and Foreman forwards the data through the Insights client to the Red Hat Hybrid Cloud Console to calculate recommendations.
-
You can view and remediate those recommendations both in the Foreman web UI and in the Red Hat Hybrid Cloud Console.
-
Foreman uploads host inventory reports to the Red Hat Hybrid Cloud Console.
-
You have control over how much information is included in those reports.
-
You cannot use local Insights in Foreman.
15.2. Prerequisites for using Insights in Red Hat Hybrid Cloud Console
Your environment must meet certain requirements before you can use Insights in the Red Hat Hybrid Cloud Console.
-
Install and configure the Insights client on hosts during host registration or provisioning. For more information, see Registering hosts by using global registration.
-
For hosts already registered to Foreman, install and configure the Insights client on your hosts by using an Ansible role. For more information, see Deploying Insights client on registered hosts.
-
You can change the schedule for running the Insights client by configuring
insights-client.timeron a host.
15.3. Configuring Foreman server for cloud connection
You can configure Foreman server to connect to the Red Hat Hybrid Cloud Console by using remote execution. This enables inventory upload and cloud-based features such as Insights for your hosts.
-
You have added the SSH key to authorized keys on your Foreman server. For more information, see the Adding Foreman server SSH key to authorized keys.
-
Your Foreman account has a role that grants the
execute_jobs_on_infrastructure_hostspermission.Note that this permission is not included in the default Remote Execution User role.
-
In the Foreman web UI, navigate to Insights > Inventory Upload.
-
Click Configure cloud connector.
-
Click Confirm.
-
In the Foreman web UI, navigate to Monitor > Foreman Tasks > Tasks.
-
Find the job with the name
Remote action: Configure cloud connector. -
Verify that the job completed successfully.
15.4. Data control settings
You can configure how Foreman handles the data collected from hosts before uploading it to the Red Hat Hybrid Cloud Console and how Foreman handles hosts in the Red Hat Hybrid Cloud Console that are no longer managed by Foreman.
15.4.1. Minimizing collected data
You can configure Foreman to use minimal reporting if you want to limit the data sent to Red Hat.
You can use minimal reporting to limit the amount of system data sent to the Subscriptions service, which remains active. Other Insights services are disabled because they require installed package data, which minimal reports do not include. Reports are still processed daily during the midnight synchronization cycle.
Minimal reports also exclude hostnames, IP addresses, and installed packages. Therefore, obfuscation and exclusion settings do not apply.
If you switch to Analytics data collection, Foreman enables the following settings by default:
-
Obfuscate host names
-
Obfuscate host ipv4 addresses
-
Exclude installed packages
Review and adjust these settings to control what data Foreman shares.
{
"report_slice_id": "de92044d-9d77-4895-83c4-a476f5020519",
"hosts": [
{
"account": "123456789",
"subscription_manager_id": "9fc621b9-08c3-4085-a749-bfed38c3052e",
"insights_id": "9fc621b9-08c3-4085-a749-bfed38c3052e",
"bios_uuid": "203F234F-58C7-4237-8DDF-A17A2838A66C",
"bios_vendor": "SeaBIOS",
"bios_version": "1.16.1-1.el9",
"arch": "x86_64",
"infrastructure_type": "virtual",
"system_profile": {
"installed_products": [
{
"name": "Red Hat Enterprise Linux for x86_64",
"id": "479"
}
],
"cores_per_socket": 1,
"system_memory_bytes": 3836579840,
"number_of_cpus": 1,
"number_of_sockets": 1
},
"cpu_socket(s)": "1"
}
]
}-
Your user account has a role that grants the
edit_settingspermission. -
Existing data in Insights Inventory has been deleted before switching to minimal reporting. To remove existing data of a system, navigate to Inventory > Systems in the Red Hat Hybrid Cloud Console, select the system, and click Delete.
-
You have selected an organization and location.
-
In the Foreman web UI, navigate to Insights > Inventory Upload.
-
Select the Minimal data collection setting from the dropdown menu under Settings.
-
When you select this option, Foreman also updates the corresponding setting on the Insights tab under Administer > Settings.
-
Click the Generate and upload report button to create a new inventory report and send it to the Red Hat Hybrid Cloud Console.
15.4.2. Obfuscating hostnames and IP addresses
You can configure Foreman to obfuscate hostnames and IP addresses when uploading host data to Insights. Obfuscation ensures that sensitive identifying information is not exposed.
When obfuscation settings are enabled, Foreman obfuscates hostnames and IP addresses.
If obfuscation settings are enabled and the host has its own insights-client obfuscation settings, Foreman honors the host settings.
If obfuscation settings are disabled, Foreman does not obfuscate hostnames or IP addresses unless the client has obfuscation enabled in insights-client.
By default, Foreman applies global obfuscation settings unless an insights-client on the host overrides the settings with its own configuration.
-
Your hosts have
insights-clientinstalled and configured.
-
In the Foreman web UI, navigate to Insights > Inventory Upload.
-
Enable the Obfuscate host names setting to obfuscate host names sent to the Red Hat Hybrid Cloud Console.
-
Enable the Obfuscate host ipv4 addresses setting to obfuscate IPv4 addresses sent to the Red Hat Hybrid Cloud Console.
-
In the Foreman web UI, navigate to Insights > Inventory Upload.
-
In the Organization dropdown menu, select the organization that uploaded the host data.
-
Click Download report to download the host inventory report from Insights.
-
Verify that the hostname is
randomhostname.example.comand the IP address is obfuscated.
15.4.3. Removing hosts from the Insights Inventory
When hosts are removed from Foreman, they can also be removed from the inventory of Insights, either automatically or manually. You can configure automatic removal of hosts from the Insights Inventory during Red Hat Hybrid Cloud Console synchronization with Foreman that occurs daily by default.
If you leave the setting disabled, you can still remove the bulk of hosts from the Inventory manually.
If Automatic mismatch deletion is enabled, Foreman removes any hosts from the Red Hat Hybrid Cloud Console that are not registered in Foreman. Enable this setting only when all hosts are registered through Foreman. If any hosts are registered through other Foreman instances or directly to the Red Hat Hybrid Cloud Console, Foreman deletes them.
-
Your Foreman account has a role that grants the
view_foreman_rh_cloudandedit_settingspermissions.
-
In the Foreman web UI, navigate to Insights > Inventory Upload.
-
Enable the Automatic mismatch deletion setting.
15.5. Enabling Insights analytics for hosts
You can enable Insights analytics for hosts. Install the Insights client on hosts to collect host data. Include hosts in the daily inventory reports uploaded to the Red Hat Hybrid Cloud Console to analyze host data.
Insights is a service by Red Hat for Red Hat Enterprise Linux hosts. Ensure to set these parameters for Red Hat Enterprise Linux hosts only. If you set the parameter on any non-Red Hat Enterprise Linux operating systems, Foreman automatically uploads new reports to the Red Hat Hybrid Cloud Console when enabled in RH Cloud Foreman settings.
You can set these parameters at any level. For more information, see Host parameter hierarchy.
-
In the Foreman web UI, navigate to Host > Provisioning Setup > Operating Systems.
-
Select any Red Hat Enterprise Linux operating systems for which you want to change the value.
-
Enable installation of the Insights client on hosts during host registration:
-
On the Parameters tab, add the
host_registration_insightsparameter, select the boolean type, and set the value to True. -
Click Submit to save the parameter.
-
-
Include the hosts in the daily inventory reports uploaded to the Red Hat Hybrid Cloud Console:
-
On the Parameters tab, add the
host_registration_insights_inventoryparameter, select the boolean type, and set the value to True. -
Click Submit to save the parameter.
-
15.6. Deploying Insights client on registered hosts
You can use the RedHatInsights.insights-client Ansible role to automate the installation of the Insights client on hosts and initiate the host data upload.
-
Remote execution with the Ansible provider is available.
-
Ensure that the following repositories are enabled on your host:
-
On Red Hat Enterprise Linux 10:
rhel-10-for-x86_64-baseos-rpmsandrhel-10-for-x86_64-appstream-rpms -
On Red Hat Enterprise Linux 9:
rhel-9-for-x86_64-baseos-rpmsandrhel-9-for-x86_64-appstream-rpms -
On Red Hat Enterprise Linux 8:
rhel-8-for-x86_64-baseos-rpmsandrhel-8-for-x86_64-appstream-rpms -
On Red Hat Enterprise Linux 7:
rhel-7-server-rpms
-
-
Add the RedHatInsights.insights-client role to the hosts. For more information, see Using Ansible roles to automate repetitive tasks on hosts in Configuring hosts by using Ansible.
-
To run the RedHatInsights.insights-client role on your host, navigate to Hosts > All Hosts and click the name of the host that you want to use.
-
On the host details page, expand the Schedule a job dropdown menu.
-
Click Run Ansible roles.
15.7. Synchronizing Insights recommendations for hosts
You can enable automatic synchronization of the recommendations from Red Hat Hybrid Cloud Console that occurs daily by default. If you leave the setting disabled, you can synchronize the recommendations manually.
-
To get the recommendations automatically:
-
In the Foreman web UI, navigate to Insights > Recommendations.
-
Enable Sync Automatically.
-
-
To get the recommendations manually:
-
In the Foreman web UI, navigate to Insights > Recommendations.
-
On the vertical ellipsis, click Sync Recommendations.
-
15.8. Examining recommendations for hosts
You can view Insights recommendations for Red Hat Enterprise Linux hosts in the Foreman web UI. Use the list to identify configuration issues and prioritize which issues to remediate.
-
In the Foreman web UI, navigate to Insights > Recommendations.
-
From the menu next to the Remediate button, select View in Insights to navigate to the recommendations page in the Red Hat Hybrid Cloud Console.
15.9. Remediating issues based on Insights recommendations
You can remediate issues on RHEL hosts based on Insights recommendations. You can only remediate recommendations that have an associated playbook.
-
In the Foreman web UI, navigate to Insights > Recommendations.
-
Select the recommendations that you want to remediate.
-
Click Remediate.
-
In the Remediation summary window, you can select the Resolutions to apply if there are multiple options. Use the Filter field to search for specific keywords.
-
Click Remediate.
-
On the Jobs page, you can view the progress of your remediation.
-
Verify that the remediation job completed successfully.
15.10. Troubleshooting Insights in Red Hat Hybrid Cloud Console
You can troubleshoot issues with Insights in the Red Hat Hybrid Cloud Console by checking logs and certificates.
To troubleshoot hosts monitoring, you can try the following approaches:
-
You can find the logs in the
/var/log/foreman/production.logfile. -
If you have problems connecting to Insights, ensure that your certificates are up-to-date. Refresh your subscription manifest to update your certificates.
16. Connecting AI applications to the MCP server for Foreman
Foreman provides a Model Context Protocol (MCP) server to enable integration with your MCP-compatible AI applications. You can obtain comprehensive AI-generated reports and data analysis of your Foreman inventory. Optionally, you can start the MCP server with permissions to edit the inventory.
|
Important
|
MCP server for Foreman is a Technology Preview feature only. Technology Preview features are not supported by Foreman community. Foreman community does not recommend using them in production. These features provide early access to upcoming product features, enabling customers to test functionality and provide feedback during the development process. |
16.1. Foreman MCP integration overview
Foreman provides a Model Context Protocol (MCP) server so that users can use their preferred AI applications to obtain and process data about Foreman inventory.
Foreman community provides a container image that you use to deploy an MCP server for Foreman. On your system, you run an AI application, also known as MCP host. Your AI application runs an MCP client. The MCP client connects to your MCP server for Foreman. The MCP server obtains the data about Foreman inventory by making API calls to your Foreman server with SSL-encrypted HTTP requests.
|
Important
|
For enhanced security, deploy the MCP server on the same system where the MCP client is running so that they can communicate over localhost. Avoid deploying the MCP server on a system exposed to the network. |
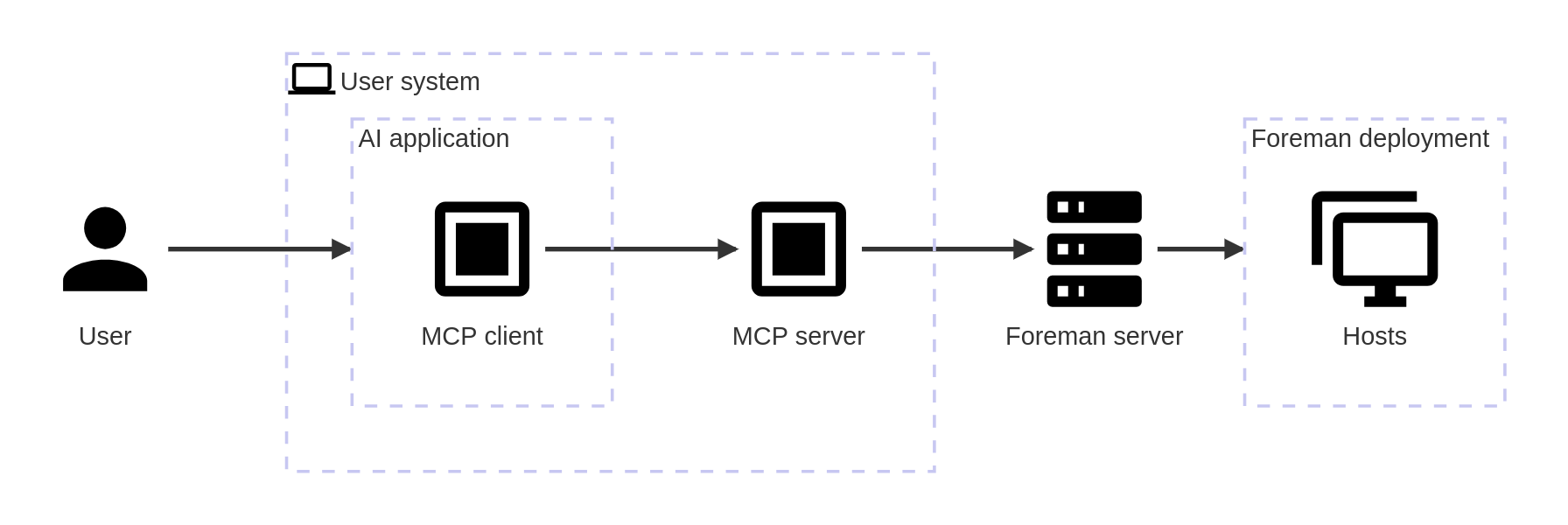
Each Foreman user deploys their own MCP server and uses their credentials to access the Foreman inventory data. A user’s MCP client cannot obtain data that the user does not have permission to access.
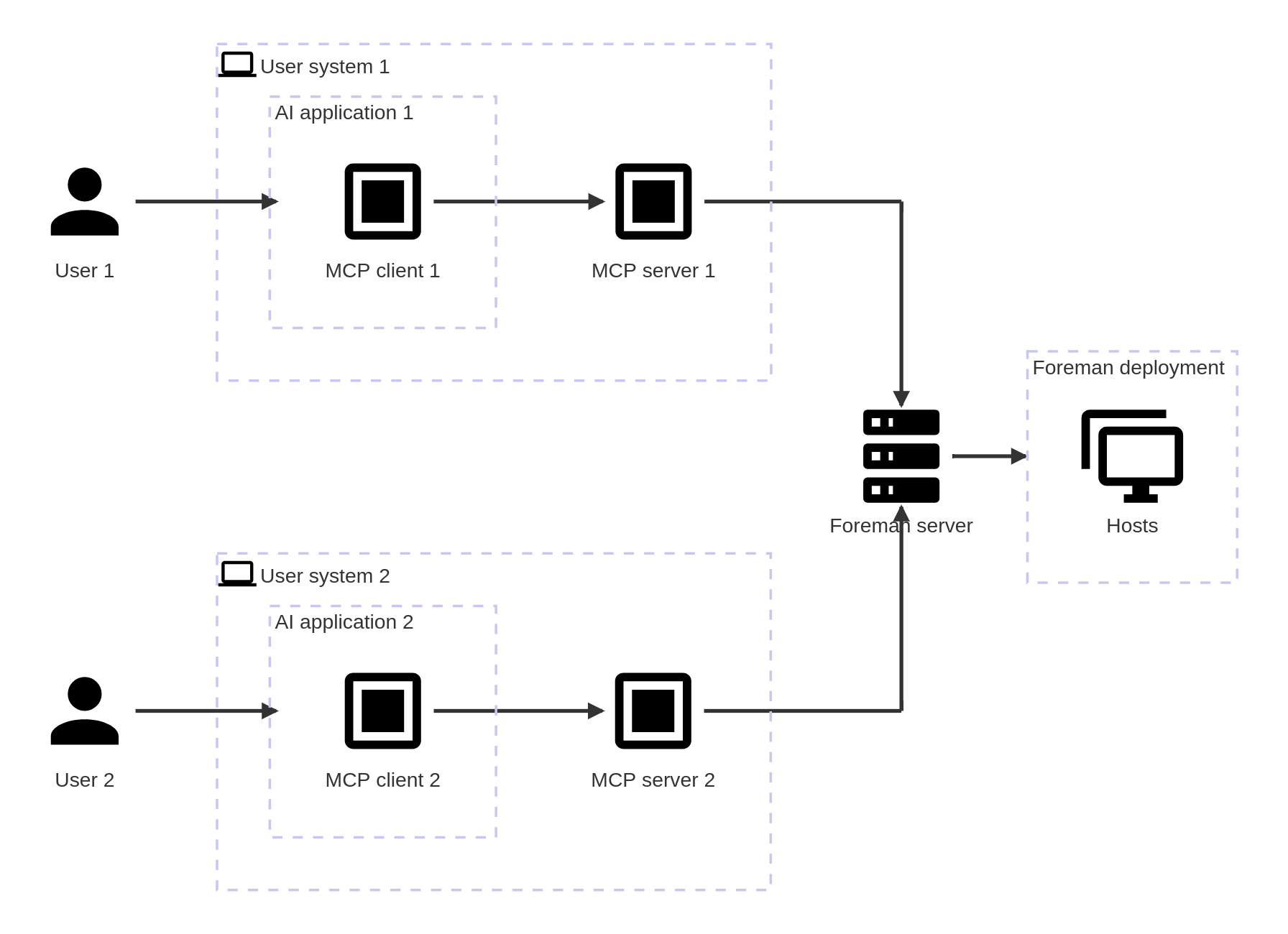
When the connection is established, you query your AI application for data about your Foreman environment. The MCP client within the AI application obtains the required data from your Foreman inventory and returns it to the AI application. The AI application processes the data to answer your queries.
The MCP server runs in read-only mode by default. It extracts data from your Foreman inventory but cannot write, edit, or make any updates to the inventory. You can start the MCP server with permissions to make changes to the inventory, for example, to start remote execution jobs or publish and promote content views.
16.2. Deploying the MCP server for Foreman
Deploy the Model Context Protocol (MCP) server for Foreman as a container and make it accessible to your MCP client.
In this scenario, you deploy the MCP server on the same system where your MCP client will run. This can also be the system Foreman server is running on.
|
Important
|
In this scenario, the MCP server uses the Streamable HTTP transport mode for client-server communication. Streamable HTTP is the default MCP transport mode that can in some cases represent potential security risks. Consider using stdio transport mode instead. For more information, see Transports in the Model Context Protocol documentation. |
-
The CA bundle for your Foreman is available on your system. You can download it from
https://foreman.example.com/unattended/public/foreman_raw_ca.
-
Optional: Pull the latest version of the MCP container image from the registry:
$ podman pull quay.io/foreman/foreman-mcp-server:latest
-
Run the container:
$ podman run --interactive --tty --publish 127.0.0.1:8080:8080 \ --volume Path_to_My_CA_Bundle:/app/ca.pem:ro,Z \ quay.io/foreman/foreman-mcp-server:latest \ --foreman-url https://foreman.example.com
The options used in the command include the following:
--publish-
Maps port 8080 from inside the container to port 8080 on the host, binding the port to the localhost.
--volume-
Mounts your CA certificate bundle from the host machine to the default location (
ca.pem) inside the container.-
romakes the read-only mode inside the container -
Zrelabels the file with a private, unshared label
-
Path_to_My_CA_Bundle-
Specifies the location of the Foreman CA bundle on the system. This is required to verify the connection to Foreman.
WarningDo not use the
--no-verify-ssloption in production environments. Disabling SSL certificate verification with--no-verify-sslcompromises the security of your connection, making you vulnerable to security threats such as man-in-the-middle (MITM) attacks.
16.3. Connecting the MCP client to the MCP server
Connect your Model Context Protocol (MCP) client to the MCP server so that your AI application can obtain data about your Foreman inventory.
In this scenario, your MCP client runs on the same system where you deployed the MCP server.
-
Your MCP client must support setting custom HTTP headers.
-
Generate a personal access token (PAT) that the MCP client will use to connect to the MCP server:
-
In the Foreman web UI, click the user menu in the top bar and select My Account.
-
Select the Personal Access Tokens tab.
-
Click Add Personal Access Token.
ImportantForeman community recommends to set an expiration date for a PAT used to configure the MCP client.
-
-
Configure your client to pass credentials in an HTTP authorization request header. The exact configuration steps depend on your MCP client.
For example, some clients require you to create a configuration file with the following contents:
"my-mcp-server": { "url": "http://localhost:8080/mcp/sse", "type": "http", "headers": { "FOREMAN_USERNAME": "My_Username", "FOREMAN_TOKEN": "My_PAT" } }
16.4. Querying the MCP server for Foreman
With your AI application connected to the Model Context Protocol (MCP) server for Foreman, you can use the AI application chatbot to request information about your Foreman deployment. The AI application retrieves and processes the relevant data from the Foreman inventory.
|
Warning
|
Always review content generated by AI before using it in production. |
Foreman community provides examples of prompts and responses below. Results in your environment and their quality might vary depending on the capabilities of the large language model (LLM) that your AI application uses.
-
Type a prompt into your AI application. For example:
Show a list of hosts that require patching.
The AI application interprets the query and asks the MCP client to retrieve the relevant data from Foreman inventory through the MCP server. The MCP client fetches the data and returns it to the AI application, which then processes it to provide an answer to the user.
- Querying hosts
-
To obtain a list of hosts that require patching and refine it, you can use the following prompts:
Show a list of hosts that require patching on my Foreman.
Categorize the list into hosts that require security patches and hosts that require bug fix patches.
- Querying subnets
-
To obtain a report of all subnets in Foreman inventory, you can use the following prompts:
Generate a static report of all subnets on my Foreman. Read API documentation for each of the needed resources before doing any searches.
For each subnet, report its name, address, network mask, and number of hosts which are assigned to it.
17. Using the KernelCare plugin
You can use the KernelCare plugin to patch the Linux kernel on hosts without rebooting them. The plugin provides job templates to view and live-patch the Linux kernel on hosts and ensures hosts do not report to Foreman server that a reboot is required through tracer.
|
Important
|
The KernelCare plugin is a technical preview. Foreman community does not recommend running this in your production environment. |
17.1. Installing the KernelCare plugin
Use the following procedure to install the KernelCare plugin.
-
Install the plugin on your Foreman server:
# foreman-installer --enable-foreman-plugin-kernel-care
17.2. KernelCare client overview
After installing the KernelCare plugin, you must provide the KernelCare client to your hosts. You synchronize the required repositories depending on the operating system of your hosts and then ensure to make the content consumable to your hosts.
17.3. KernelCare client repositories
The following tables list KernelCare client repositories for supported client operating systems. Each table corresponds to a product name and each row corresponds to a repository name.
- Prerequisites
-
-
Import the GPG public into Foreman.
-
For Yum content, import https://repo.cloudlinux.com/kernelcare/RPM-GPG-KEY-KernelCare.
-
For Deb content, import https://repo.cloudlinux.com/kernelcare/kernelcare.gpg.
For more information, see Importing a GPG key by using Foreman web UI in Managing content.
-
-
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL | Releases/Distributions | Components | Architectures |
|---|---|---|---|---|
|
|
|
|
| Name | Upstream URL | Releases/Distributions | Components | Architectures |
|---|---|---|---|---|
|
|
|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL |
|---|---|
|
| Name | Upstream URL | Releases/Distributions | Components | Architectures |
|---|---|---|---|---|
|
|
|
|
| Name | Upstream URL | Releases/Distributions | Components | Architectures |
|---|---|---|---|---|
|
|
|
|
| Name | Upstream URL | Releases/Distributions | Components | Architectures |
|---|---|---|---|---|
|
|
|
|
17.4. Installing the KernelCare package on hosts
You can use kernelcare to patch the Linux kernel on hosts without rebooting them.
-
Your hosts have access to the KernelCare repository. For more information, see KernelCare client overview.
-
In the Foreman web UI, navigate to Monitor > Jobs and click Run job.
-
Select Katello as Job category and Install Package – Katello Script Default as Job template and click Next.
-
Select hosts on which you want to run the job. If you do not select any hosts, the job will run on all hosts you can see in the current context.
-
In the package field, enter
kernelcareand click Next. -
Optional: To configure advanced settings for the job, fill in the Advanced fields. To learn more about advanced settings, see Advanced settings in the job wizard.
-
Click Next.
-
Select Immediate execution to execute the job immediately and click Next.
-
Review job details. You have the option to return to any part of the job wizard and edit the information.
-
Click Run to install
kernelcareon your hosts.
17.5. Viewing patched kernel version
You can use a job template to view the patched kernel version on hosts.
-
The
kernelcarepackage is installed on your hosts. For more information, see Installing the KernelCare package on hosts.
-
In the Foreman web UI, navigate to Monitor > Jobs and click Run job.
-
Select LivePatching – Script Default as Job category and LivePatching – Kernel version as Job template and click Next.
-
Select hosts on which you want to run the job. If you do not select any hosts, the job will run on all hosts you can see in the current context.
-
Click Next.
-
Optional: To configure advanced settings for the job, fill in the Advanced fields. To learn more about advanced settings, see Advanced settings in the job wizard.
-
Click Next.
-
Select Immediate execution to execute the job immediately and click Next.
-
Review job details. You have the option to return to any part of the job wizard and edit the information.
-
Click Run to view the running Kernel version on your hosts.
17.6. Live patching hosts using KernelCare plugin
You can use kcarectl provided by TuxCare to live-patch the Linux kernel on your hosts.
By default, kcarectl checks for updates every four hours.
If the automatic installation of patches is disabled or if you want to install patches manually at a certain time, you can start the process using a remote execution job.
-
Your hosts have the
kernelcarepackage installed. -
Your hosts have internet access to connect to cloudlinux.com.
If your host is in a disconnected environment, you can use ePortal by Tuxcare to provide Linux kernel patches. For more information, see docs.tuxcare.com/eportal.
-
In the Foreman web UI, navigate to Monitor > Jobs and click Run job.
-
Select LivePatching – Script Default as Job category and LivePatching – Update kernel as Job template and click Next.
-
Select hosts on which you want to run the job. If you do not select any hosts, the job will run on all hosts you can see in the current context.
-
Click Next.
-
Optional: To configure advanced settings for the job, fill in the Advanced fields. To learn more about advanced settings, see Advanced settings in the job wizard.
-
Click Next.
-
Select Immediate execution to execute the job immediately and click Next.
-
Review job details. You have the option to return to any part of the job wizard and edit the information.
-
Click Run to update to the latest Linux kernel on your hosts.
18. Using report templates to monitor hosts
You can use report templates to query Foreman data to obtain information about, for example, host status, registered hosts, applicable errata, applied errata, and user activity. You can use the report templates that ship with Foreman or write your own custom report templates to suit your requirements.
18.1. Generating host monitoring reports by using Foreman web UI
You can generate host monitoring reports from the Foreman web UI so that you can view host data, such as installed packages or compliance status, in a report template. You can also schedule reports or send them by e-mail.
-
In the Foreman web UI, navigate to Monitor > Reports > Report Templates. For example, the Host – Installed Products template generates a report with installed product information along with other metrics, including system purpose attributes.
-
To the right of the report template that you want to use, click Generate.
-
Optional: To schedule a report, to the right of the Generate at field, click the icon to select the date and time you want to generate the report at.
-
Optional: To send a report to an e-mail address, select the Send report via e-mail checkbox, and in the Deliver to e-mail addresses field, enter the required e-mail address.
-
Optional: Apply search query filters. To view all available results, do not populate the filter field with any values.
-
Click Submit. A CSV file that contains the report is downloaded. If you have selected the Send report via e-mail checkbox, the host monitoring report is sent to your e-mail address.
18.2. Generating host monitoring reports by using Hammer CLI
You can generate host monitoring reports by using Hammer CLI so that you can view host data, such as installed packages or compliance status, in a report template. To schedule reports, configure a cron job.
-
List all available report templates:
$ hammer report-template list
-
Generate a report:
$ hammer report-template generate --id My_Template_ID
This command waits until the report fully generates before completing. If you want to generate the report as a background task, you can use the
hammer report-template schedulecommand.
To generate the Subscription - General report, add the Days from Now option to specify the latest expiration time of general subscriptions.
-
To show all subscriptions:
$ hammer report-template generate \ --inputs "Days from Now=no limit" \ --name "Subscription - General Report"
-
To show all subscriptions that are going to expire within 60 days:
$ hammer report-template generate \ --inputs "Days from Now=60" \ --name "Subscription - General Report"
18.3. Creating a report template
In Foreman, you can create a report template and customize the template to suit your requirements. You can import existing report templates and further customize them with snippets and template macros.
Report templates use Embedded Ruby (ERB) syntax. To view information about working with ERB syntax and macros, in the Foreman web UI, navigate to Monitor > Reports > Report Templates, and click Create Template, and then click the Help tab.
When you create a report template in Foreman, safe mode is enabled by default.
-
In the Foreman web UI, navigate to Monitor > Reports > Report Templates.
-
Click Create Template.
-
In the Name field, enter a unique name for your report template.
-
If you want the template to be available to all locations and organizations, select Default.
-
Create the template directly in the template editor or import a template from a text file by clicking Import. For more information about importing templates, see Importing report templates.
-
Optional: In the Audit Comment field, you can add any useful information about this template.
-
Click the Input tab, and in the Name field, enter a name for the input that you can reference in the template in the following format:
input('name'). Note that you must save the template before you can reference this input value in the template body. -
Select whether the input value is mandatory. If the input value is mandatory, select the Required checkbox.
-
From the Value Type list, select the type of input value that the user must input.
-
Optional: If you want to use facts for template input, select the Advanced checkbox.
-
Optional: In the Options field, define the options that the user can select from. If this field remains undefined, the users receive a free-text field in which they can enter the value they want.
-
Optional: In the Default field, enter a value, for example, a host name, that you want to set as the default template input.
-
Optional: In the Description field, you can enter information that you want to display as inline help about the input when you generate the report.
-
Optional: Click the Type tab, and select whether this template is a snippet to be included in other templates.
-
Click the Location tab and add the locations where you want to use the template.
-
Click the Organizations tab and add the organizations where you want to use the template.
-
Click Submit to save your changes.
18.4. Exporting report templates by using Foreman web UI
You can export report templates that you create in Foreman from Foreman web UI.
-
In the Foreman web UI, navigate to Monitor > Reports > Report Templates.
-
Locate the template that you want to export, and from the list in the Actions column, select Export.
-
Repeat this action for every report template that you want to download.
18.5. Exporting report templates by using Hammer CLI
You can export report templates that you create in Foreman by using Hammer CLI.
-
To view the report templates available for export, enter the following command:
$ hammer report-template list
Note the template ID of the template that you want to export in the output of this command.
-
To export a report template, enter the following command:
$ hammer report-template dump --id My_Template_ID > example_export.erb
18.6. Exporting report templates using the Foreman API
You can use the Foreman report_templates API to export report templates from Foreman.
-
Use the following request to retrieve a list of available report templates. For example:
$ curl \ --user "My_User_Name:My_Password" \ https://foreman.example.com/api/report_templates \ | json_reformat
In this example, the
json_reformattool is used to format the JSON output.Example response:
{ "total": 6, "subtotal": 6, "page": 1, "per_page": 20, "search": null, "sort": { "by": null, "order": null }, "results": [ { "created_at": "2019-11-20 17:49:52 UTC", "updated_at": "2019-11-20 17:49:52 UTC", "name": "Applicable errata", "id": 112 }, { "created_at": "2019-11-20 17:49:52 UTC", "updated_at": "2019-11-20 17:49:52 UTC", "name": "Applied Errata", "id": 113 }, { "created_at": "2019-11-30 16:15:24 UTC", "updated_at": "2019-11-30 16:15:24 UTC", "name": "Hosts - complete list", "id": 158 }, { "created_at": "2019-11-20 17:49:52 UTC", "updated_at": "2019-11-20 17:49:52 UTC", "name": "Host statuses", "id": 114 }, { "created_at": "2019-11-20 17:49:52 UTC", "updated_at": "2019-11-20 17:49:52 UTC", "name": "Registered hosts", "id": 115 }, { "created_at": "2019-11-20 17:49:52 UTC", "updated_at": "2019-11-20 17:49:52 UTC", "name": "Subscriptions", "id": 116 } ] } -
Note the
idof the template that you want to export, and use the following request to export the template.Example request:
$ curl \ --output /tmp/_Example_Export_Template.erb_ \ --user "My_User_Name:My_Password" \ https://foreman.example.com/api/report_templates/My_Template_ID/export
In this example, the exported template is redirected to
host_complete_list.erb.
18.7. Importing report templates
You can import a report template into the body of a new template that you want to create. Note that using the Foreman web UI, you can only import templates individually.
-
Templates are exported from Foreman for use in new templates. For more information see Exporting report templates by using Foreman web UI and Exporting report templates by using Hammer CLI.
-
In the Foreman web UI, navigate to Monitor > Reports > Report Templates.
-
In the upper right of the Report Templates window, click Create Template.
-
On the upper right of the Editor tab, click the folder icon, and select the
.erbfile that you want to import. -
Edit the template to suit your requirements.
-
Click Submit.
18.8. Importing report templates using the Foreman API
You can use the Foreman API to import report templates into Foreman. Importing report templates using the Foreman API automatically parses the report template metadata and assigns organizations and locations.
-
A template is created using
.erbsyntax or exported from another Foreman.For more information about writing templates, see Template writing reference.
For more information about exporting templates from Foreman, see Exporting report templates using the Foreman API.
-
Use the following example to format the template that you want to import to a
.jsonfile:# cat Example_Template.json { "name": "Example Template Name", "template": " Enter ERB Code Here " }Example JSON file with ERB template:
{ "name": "Hosts - complete list", "template": " <%# name: Hosts - complete list snippet: false template_inputs: - name: host required: false input_type: user advanced: false value_type: plain resource_type: Katello::ActivationKey model: ReportTemplate -%> <% load_hosts(search: input('host')).each_record do |host| -%> <% report_row( 'Server FQDN': host.name ) -%> <% end -%> <%= report_render %> " } -
Use the following request to import the template:
$ curl \ --data @Example_Template.json \ --header "Content-Type: application/json" \ --request POST \ --user "My_User_Name:My_Password" \ https://foreman.example.com/api/report_templates/import
-
Use the following request to retrieve a list of report templates and validate that you can view the template in Foreman:
$ curl \ --user "My_User_Name:My_Password" \ https://foreman.example.com/api/report_templates \ | json_reformat
18.9. Report template safe mode
When you create report templates in Foreman, report template safe mode is enabled by default. Safe mode helps prevent rendering problems and enforces best practices in report templates.
Report template safe mode limits the macros and variables that you can use in the report template. The list of supported macros and variables is available in the Foreman web UI.
To view the macros and variables that are available, in the Foreman web UI, navigate to Monitor > Reports > Report Templates and click Create Template. In the Create Template window, click the Help tab and expand Safe mode methods.
While safe mode is enabled, if you try to use a macro or variable that is not listed in Safe mode methods, the template editor displays an error message.
To view the status of safe mode in Foreman, in the Foreman web UI, navigate to Administer > Settings and click the Provisioning tab. Locate the Safemode rendering row to check the value.
19. Configuring host collections
To group hosts and perform the same action on them at once, you can use host collections. Available actions include managing packages, applying errata, or assigning content view environments. Group hosts in a way that suits your workflow, such as by function, department, or business unit.
19.1. Creating a host collection by using Foreman web UI
You can create a host collection from the Foreman web UI to group hosts and perform bulk actions such as package updates or errata installation.
-
Your user account has a role that grants the
create_host_collectionspermission.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Click New Host Collection.
-
Add the Name of the host collection.
-
Clear Unlimited Hosts, and enter the desired maximum number of hosts in the Limit field.
-
Add the Description of the host collection.
-
Click Save.
19.2. Creating a host collection by using Hammer CLI
You can create a host collection by using Hammer CLI to group hosts and perform bulk actions such as package updates or errata installation.
-
Create a host collection:
$ hammer host-collection create \ --name "My_Host_Collection" \ --organization "My_Organization"
19.3. Cloning a host collection
You can clone a host collection to create a new collection with the same settings and membership, then adjust it as needed.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
On the left hand panel, click the host collection you want to clone.
-
Click Copy Collection.
-
Specify a name for the cloned collection.
-
Click Create.
19.4. Removing a host collection
You can remove a host collection from Foreman when you no longer need that grouping. The hosts in the collection are not deleted.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Select the host collection that you want to remove.
-
Under Select Action, click Remove.
-
Click Delete to remove the host collection.
19.5. Adding a host to a host collection by using Foreman web UI
You can add a host to a host collection from the Foreman web UI.
Note that if you add a host to a host collection, the Foreman auditing system does not log the change.
-
A host must be registered to Foreman to add it to a Host Collection. For more information about registering hosts, see Registering hosts by using global registration.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of the host you want to modify.
-
In the Host collections card, click the vertical ellipsis and select Add host to collections.
-
Select the host collection.
-
Click Add.
19.6. Adding a host to a host collection by using Hammer CLI
You can add a host to a host collection by using Hammer CLI.
Note that if you add a host to a host collection, the Foreman auditing system does not log the change.
-
A host must be registered to Foreman to add it to a Host Collection. For more information about registering hosts, see Registering hosts by using global registration.
-
Add a host to your host collection:
$ hammer host-collection add-host \ --host-ids My_Host_ID \ --id My_Host_Collection_ID
19.7. Adding hosts to a host collection in bulk by using Foreman web UI
You can add multiple hosts to a host collection at once from the Foreman web UI.
Note that if you add a host to a host collection, the Foreman auditing system does not log the change.
-
A host must be registered to Foreman to add it to a host collection. For more information about registering hosts, see Registering hosts by using global registration.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Select the host collection where the host should be added.
-
On the Hosts tab, select the Add subtab.
-
Select the hosts to be added from the table and click Add Selected.
19.8. Adding hosts to a host collection in bulk by using Hammer CLI
You can add multiple hosts to a host collection at once by using Hammer CLI.
Note that if you add a host to a host collection, the Foreman auditing system does not log the change.
-
A host must be registered to Foreman to add it to a host collection. For more information about registering hosts, see Registering hosts by using global registration.
-
Add multiple hosts to a host collection:
$ hammer host-collection add-host \ --host-ids My_Host_ID_1,My_Host_ID_2 \ --id My_Host_Collection_ID
19.9. Removing a host from a host collection
Remove hosts from a host collection to update membership without deleting the host from Foreman.
Note that if you remove a host from a host collection, the host collection record in the database is not modified so the Foreman auditing system does not log the change.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Choose the desired host collection.
-
On the Hosts tab, select the List/Remove subtab.
-
Select the hosts you want to remove from the host collection and click Remove Selected.
19.10. Managing host content with host collections
You can use host collections in Foreman to install packages, apply errata, or manage other content across all hosts in the collection.
19.10.1. Installing packages on hosts in a host collection
You can install packages on all hosts in a host collection in one action.
-
The packages or package groups you want to install should be available in one of the existing repositories or added before this procedure.
-
Content should be promoted to the environment where the hosts are assigned.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Select the host collection on which you want to install the package.
-
On the Collection Actions tab, click Package Installation, Removal, and Update.
-
To update all packages, click Update All Packages to use the default method. Alternatively, select the drop-down icon to the right of the button to select a method to use. Selecting the via remote execution – customize first menu entry will take you to the Job invocation page where you can customize the action.
-
Select the Package or Package Group radio button as required.
-
In the field provided, specify the package or package group name. Then click:
-
Install – to install a new package using the default method. Alternatively, select the drop-down icon to the right of the button and select a method to use. Selecting the via remote execution – customize first menu entry will take you to the Job invocation page where you can customize the action.
-
Update – to update an existing package in the host collection using the default method. Alternatively, select the drop-down icon to the right of the button and select a method to use. Selecting the via remote execution – customize first menu entry will take you to the Job invocation page where you can customize the action.
-
19.10.2. Viewing installed packages
You can view the installed packages on a host to see what is present or to plan package or errata actions.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select the name of the host.
-
On the Content tab, Packages displays a list of installed packages.
-
To see details of a package, select that package.
-
The Details tab displays details of the selected package.
-
The Files tab lists the files contained in the package.
-
The Dependencies tab lists the dependencies of the package.
-
The Repositories tab lists the repositories that contain the selected package.
-
-
You can filter these by Library or Default organization.
19.10.3. Upgrading a package
You can upgrade an installed package on a host to a newer version from the Foreman web UI to get bug fixes or new features.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select the name of the host that contains the package you want to upgrade.
-
On the Content tab, select Packages.
The Status column displays whether the package is upgradable or Up-to date. You cannot update an up-to-date package.
-
From the list of packages, choose the package you want to upgrade and click the vertical ellipsis icon at the end of the line.
-
Choose the Apply via Remote Execution to use Remote Execution, or Apply via customized remote execution if you want to customize the remote execution, for example, to set a time when it should be applied.
-
Click Submit to upgrade the package.
19.10.4. Removing a package from a host
To uninstall software or resolve dependency issues, you can remove a package from a host.
-
In the Foreman web UI, navigate to Hosts > All Hosts and select the host containing the package you want to remove.
-
On the Content tab, select Packages.
-
Click the vertical ellipsis icon at the end of the line for the package you want to remove, and choose the Remove option.
-
Click Submit.
19.10.5. Applying errata to hosts in a host collection
You can apply errata to all hosts in a host collection in one action using remote execution.
-
The errata to be applied should be available in one of the existing repositories, or the repository should be enabled on the host before this procedure.
-
Errata should be promoted to the environment where the hosts are assigned.
-
In the Foreman web UI, navigate to Hosts > Host Collections.
-
Select the host collection where the errata should be applied.
-
On the Collection Actions tab, click Errata Installation.
-
Select the errata you want to apply to the hosts in the collection and click Install Selected to use the default method. Alternatively, select the drop-down icon to the right of the button to select a method to use. Selecting the via remote execution – customize first menu entry takes you to the Job invocation page where you can customize the action.
19.10.6. Applying errata to a host
To patch security vulnerabilities and bugs, you can apply errata to a host.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the host you want to apply errata to.
-
Click Content and select the Errata tab.
-
Select the errata you want to apply to the host, or select the checkbox at the top of the list to apply all installable errata. Click the checkbox next to any errata you want to remove from a full list.
-
Using the vertical ellipsis icon next to the errata you want to apply to the host, select Apply via Remote Execution to use Remote Execution, or select Apply via customized remote execution if you want to customize the remote execution.
-
Click Submit.
19.10.7. Applying errata to hosts by using Foreman web UI
You can use the Foreman web UI to review and apply errata to hosts so that security and bugfix updates are installed on selected hosts.
-
In the Foreman web UI, navigate to Content > Content Types > Errata.
-
Click the name of an erratum you want to apply.
-
On the to Content Hosts tab, select all hosts that you want to apply errata to.
-
Click Apply to Hosts and click Confirm.
-
In the Foreman web UI, navigate to Monitor > Jobs.
-
Select the most recent
Install erratajob. -
Verify that the remote execution to apply errata to all selected host succeeded.
19.10.8. Filter errata by type and severity
You can filter errata by type or severity to focus on security updates, bug fixes, or enhancements when planning or applying errata.
-
In the Foreman web UI, navigate to Hosts > All Hosts and click the name of the host.
-
On the Contents tab, Errata lists the errata associated with the selected host.
-
Click Type to filter errata by type.
-
You can filter to display errata of type Security, Bugfix, or Enhancement
-
Click Severity to filter by severity.
-
You can filter to display errata of severity N/A, Low, Moderate, Important, or Critical.
-
To deselect your choice, return to the list of options and click the selected option again.
You can also use the Errata card on the host page to pre-filter errata for type before display.
19.10.9. Viewing errata by applicable and installable
You can view errata by applicable or installable status to see which updates affect your hosts and which are ready to install.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select the host name.
-
Click the Overview tab. Under the Errata card, there are two types of Errata.
-
Click Applicable to view errata that apply to a package installed on your host.
-
Click Installable to view applicable errata that are available in the content view environments of the host.
-
Click the link with number of errata under each type to see the list of all available errata of that type.
-
Click security advisories, bug fixes, or enhancements under each type to view only the respective type of errata.
19.10.10. Generating a report for installable and applicable errata
You can generate a report of installable or applicable errata on hosts to review update status across your environment before applying errata.
-
In the Foreman web UI, navigate to Monitor > Reports > Report Templates.
-
Click Generate for the Host – Applicable Errata template.
-
Optional: To schedule a report, click the calendar icon to the right of the Generate at field and choose the date and time you want for the generated report.
-
Optional: To send a report to an e-mail address, select the Send report via e-mail checkbox, and in the Deliver to e-mail addresses field, enter the required e-mail address.
-
Optional: Select another Output format for the report file. The default is CSV.
-
Optional: To limit the report only to hosts found by the search query, click on Hosts filter and search from the available list of hosts. For a report on all available hosts, leave Hosts filter empty.
-
Optional: To limit the report only to errata found by the search query, click on Errata filter and search from the available list of errata. For a report on all available errata, leave Errata filter empty.
-
From the Installability list, select one of these options:
-
Applicable to show all applicable errata.
-
Installable to limit the report exclusively to errata that are accessible in the content view environments of your host that may be installed.
-
-
Click Generate. Your browser automatically downloads the report file after Foreman creates it. If you have selected the Send report via e-mail option, the report is sent to your e-mail address.
19.10.11. Removing content from hosts in a host collection
Remove packages or package groups from hosts in a host collection to keep collection content in sync with your requirements.
-
Click Hosts > Host Collections.
-
Click the host collection where the package should be removed.
-
On the Collection Actions tab, click Package Installation, Removal, and Update.
-
Select the Package or Package Group radio button as required.
-
In the field provided, specify the package or package group name.
-
Click Remove to remove the package or package group using the default method. Alternatively, select the drop-down icon to the right of the button and select a method to use. Selecting the via remote execution - customize first menu entry will take you to the Job invocation page where you can customize the action.
19.10.12. Changing the lifecycle environment or content view of a host collection
You can change the lifecycle environment or content view assigned to a host collection so that all hosts in the host collection consume content from the new lifecycle environment or content view.
-
In the Foreman web UI, navigate to Hosts > Host Collection.
-
Selection the host collection where the lifecycle environment or content view should be changed.
-
On the Collection Actions tab, click Change assigned Lifecycle Environment or Content View.
-
Select the lifecycle environment to be assigned to the host collection.
-
Select the required content view from the list.
-
Click Assign.
NoteThe changes take effect in approximately 4 hours. To make the changes take effect immediately, on the host, enter the following command:
# subscription-manager refresh
You can use remote execution to run this command on multiple hosts at the same time.
20. Configuring and setting up remote jobs
Foreman supports remote execution of commands on hosts. Using remote execution, you can perform various tasks on multiple hosts simultaneously.
20.1. Remote execution overview
With remote execution in Foreman, you can run commands on hosts from Smart Proxies by using shell scripts or Ansible. Multiple transport modes and job providers are available so that you can pick the one that fits your environment.
20.1.1. Remote execution in Foreman
With remote execution, you can run jobs on hosts from Smart Proxies by using shell scripts or Ansible roles and playbooks.
Use remote execution for the following benefits in Foreman:
-
Run jobs on multiple hosts at once.
-
Use variables in your commands for more granular control over the jobs you run.
-
Use host facts and parameters to populate the variable values.
-
Specify custom values for templates when you run the command.
Communication for remote execution occurs through Smart Proxy server, which means that Foreman server does not require direct access to the target host, and can scale to manage many hosts.
To use remote execution, you must define a job template. A job template is a command that you want to apply to remote hosts. You can execute a job template multiple times.
Foreman uses ERB syntax job templates.
By default, Foreman includes several job templates for shell scripts and Ansible.
20.1.2. Remote execution workflow
When you run a remote job on hosts, Foreman uses various strategies to select a remote execution Smart Proxy for each host to balance the load across available Smart Proxies. Knowing how Foreman selects a Smart Proxy helps you configure subnets and proxy assignments so remote jobs use the proxy you intend, and recognize why a job ran on a particular proxy.
For custom Ansible roles that you create, or roles that you download, you must install the package containing the roles on your Smart Proxy server. Before you can use Ansible roles, you must import the roles into Foreman from the Smart Proxy where they are installed.
Foreman searches only for Smart Proxies that have the remote execution feature enabled.
-
Foreman finds the host’s interfaces that have the Remote execution checkbox selected.
-
Foreman finds the subnets of these interfaces.
-
Foreman finds remote execution Smart Proxies assigned to these subnets.
-
From this set of Smart Proxies, Foreman selects the Smart Proxy that has the least number of running jobs. By doing this, Foreman ensures that the jobs load is balanced between remote execution Smart Proxies.
If you have enabled Prefer registered through Smart Proxy for remote execution, Foreman runs the REX job by using the Smart Proxy to which the host is registered.
By default, Prefer registered through Smart Proxy for remote execution is set to No.
To enable it, in the Foreman web UI, navigate to Administer > Settings, and on the Content tab, set Prefer registered through Smart Proxy for remote execution to Yes.
This ensures that Foreman performs REX jobs on hosts by the Smart Proxy to which they are registered to.
If Foreman does not find a remote execution Smart Proxy at this stage, and if the Fallback to Any Smart Proxy setting is enabled, Foreman adds another set of Smart Proxies to select the remote execution Smart Proxy from. Foreman selects the most lightly loaded Smart Proxy from the following types of Smart Proxies that are assigned to the host:
-
DHCP, DNS and TFTP Smart Proxies assigned to the host’s subnets
-
DNS Smart Proxy assigned to the host’s domain
-
Realm Smart Proxy assigned to the host’s realm
-
Puppet server Smart Proxy
-
Puppet CA Smart Proxy
-
OpenSCAP Smart Proxy
If Foreman does not find a remote execution Smart Proxy at this stage, and if the Enable Global Smart Proxy setting is enabled, Foreman selects the most lightly loaded remote execution Smart Proxy from the set of all Smart Proxies in the host’s organization and location to execute a remote job.
20.1.3. Transport modes for remote execution
You can configure Foreman to use push-based (SSH) or pull-based (MQTT) transport for remote job execution. Each Smart Proxy uses one mode. Choose push for slightly better scalability in larger deployments or pull if your organization restricts the ports needed for SSH.
- Push-based transport
-
On Smart Proxies in
sshmode, remote execution uses the SSH service to transport job details. This is the default transport mode. The SSH service must be enabled and active on the target hosts. The remote execution Smart Proxy must have access to the SSH port on the target hosts. Unless you have a different setting, the standard SSH port is 22.This transport mode supports both Script and Ansible providers.
- Pull-based transport
-
On Smart Proxies in
pull-mqttmode, remote execution uses Message Queueing Telemetry Transport (MQTT) to initiate the job execution it receives from Foreman server. The host subscribes to the MQTT broker on Smart Proxy for job notifications by using theyggdrasilpull client. After the host receives a notification from the MQTT broker, it pulls job details from Smart Proxy over HTTPS, runs the job, and reports results back to Smart Proxy.This transport mode supports the Script provider only.
To use the
pull-mqttmode, you must enable it on Smart Proxy server and configure the pull client on hosts.
|
Note
|
If your Smart Proxy already uses the # foreman-installer --foreman-proxy-plugin-remote-execution-script-mode ssh |
20.2. Getting started with remote execution
To run your first remote job, ensure that your user account has the required permissions and your hosts are configured to run remote jobs.
20.2.1. Permissions for remote execution
You can control which roles can run which jobs within your infrastructure, including which hosts they can target.
The remote execution feature provides two built-in roles:
-
Remote Execution Manager: Can access all remote execution features and functionality.
-
Remote Execution User: Can only run jobs.
You can clone the Remote Execution User role and customize its filter for increased granularity.
If you adjust the filter with the view_job_templates permission on a customized role, you can only see and trigger jobs based on matching job templates.
You can use the view_hosts and view_smart_proxies permissions to limit which hosts or Smart Proxies are visible to the role.
The execute_template_invocation permission is a special permission that is checked immediately before execution of a job begins.
This permission defines which job template you can run on a particular host.
This allows for even more granularity when specifying permissions.
You can run remote execution jobs against Foreman and Smart Proxy registered as hosts to Foreman with the execute_jobs_on_infrastructure_hosts permission.
Standard Manager and Site Manager roles have this permission by default.
If you use either the Manager or Site Manager role, or if you use a custom role with the execute_jobs_on_infrastructure_hosts permission, you can execute remote jobs against registered Foreman and Smart Proxy hosts.
For more information on working with roles and permissions, see Creating and managing roles in Administering Foreman.
The following example shows filters for the execute_template_invocation permission:
name = Reboot and host.name = staging.example.com name = Reboot and host.name ~ *.staging.example.com name = "Restart service" and host_group.name = webservers
Use the first line in this example to apply the Reboot template to one selected host.
Use the second line to define a pool of hosts with names ending with .staging.example.com.
Use the third line to bind the template with a host group.
|
Note
|
Permissions assigned to users with these roles can change over time. If you have already scheduled some jobs to run in the future, and the permissions change, this can result in execution failure because permissions are checked immediately before job execution. |
20.2.2. Configuring a host to use the pull client
For Smart Proxies configured to use pull-mqtt mode, hosts can subscribe to remote jobs using the remote execution pull client.
This does not use SSH and hosts do not require opening up any incoming firewall ports.
-
You have registered the host to Foreman.
-
The Smart Proxy through which the host is registered is configured to use
pull-mqttmode. For more information, see Configuring pull-based transport for remote execution in Installing a Smart Proxy Server nightly on Enterprise Linux. -
Foreman Client repository for the operating system version of the host is synchronized on Foreman server, available in the content view and the lifecycle environment of the host, and enabled for the host. For more information, see Changing the repository sets status for a host in Foreman in Managing content.
-
Your host has access to the default operating system repositories.
-
The host can communicate with its Smart Proxy over MQTT using port
1883. -
The host can communicate with its Smart Proxy over HTTPS using port
9090.
-
Install the
katello-pull-transport-migratepackage on your host:-
On Enterprise Linux 10, Enterprise Linux 9, and Enterprise Linux 8 hosts:
# dnf install katello-pull-transport-migrate
-
On Debian/Ubuntu hosts:
# apt install katello-pull-transport-migrate
-
On SUSE Linux Enterprise Server hosts:
# zypper install katello-pull-transport-migrate
-
-
Determine which version of the
yggdrasilpackage is installed on the host:-
On Enterprise Linux and SUSE Linux Enterprise Server hosts:
$ rpm --query yggdrasil
-
On Debian/Ubuntu hosts:
$ dpkg-query --show yggdrasil-mqtt
-
-
Check the status of the Yggdrasil services:
-
If your host has
yggdrasilversion 0.4.z or later installed:# systemctl status yggdrasil com.redhat.Yggdrasil1.Worker1.foreman
-
If your host has
yggdrasilversion 0.2.z or earlier installed:# systemctl status yggdrasild
-
If the services are running, you have successfully configured the host to use the pull client.
20.2.3. Distributing SSH keys for remote execution
For Smart Proxies in ssh mode, remote execution connections are authenticated using SSH.
The public SSH key from Smart Proxy must be distributed to its attached hosts that you want to manage.
Foreman distributes SSH keys for the remote execution feature to the hosts provisioned from Foreman by default.
-
The SSH service is enabled and running on the hosts.
-
Any network or host-based firewalls are configured to enable access to port 22.
-
If the hosts are running on Amazon Web Services, enable password authentication. For more information, see New User Accounts.
-
Use one of the following methods to distribute the public SSH key from Smart Proxy to target hosts:
-
Using the Foreman API to obtain SSH keys for remote execution.
-
Configuring a Kickstart template to distribute SSH keys during provisioning.
-
For new Foreman hosts, you can deploy SSH keys to Foreman hosts during registration using the global registration template. For more information, see Registering hosts by using global registration in Managing hosts.
20.2.4. Executing a remote job by using Foreman web UI
You can execute a job that is based on a job template against one or more hosts from the Foreman web UI.
|
Note
|
Ansible jobs run in batches on multiple hosts, so you cannot cancel a job running on a specific host. A job completes only after the Ansible Playbook runs on all hosts in the batch. |
-
In the Foreman web UI, navigate to Monitor > Jobs and click Run job.
-
Select the Job category and the Job template you want to use, then click Next.
-
Select hosts on which you want to run the job. If you do not select any hosts, the job will run on all hosts you can see in the current context.
NoteIf you want to select a host group and all of its subgroups, it is not sufficient to select the host group as the job would only run on hosts directly in that group and not on hosts in subgroups. Instead, you must either select the host group and all of its subgroups or use this search query:
hostgroup_fullname ~ "My_Host_Group*"
Replace My_Host_Group with the name of the top-level host group.
-
If required, provide inputs for the job template. Different templates have different inputs and some templates do not have any inputs. After entering all the required inputs, click Next.
-
Optional: To configure advanced settings for the job, fill in the Advanced fields. To learn more about advanced settings, see Advanced settings in the job wizard.
-
Click Next.
-
Schedule time for the job.
-
To execute the job immediately, keep the pre-selected Immediate execution.
-
To execute the job in future time, select Future execution.
-
To execute the job on regular basis, select Recurring execution.
-
-
Optional: If you selected future or recurring execution, select the Query type, otherwise click Next.
-
Static query means that job executes on the exact list of hosts that you provided.
-
Dynamic query means that the list of hosts is evaluated just before the job is executed. If you entered the list of hosts based on some filter, the results can be different from when you first used that filter.
Click Next after you have selected the query type.
-
-
Optional: If you selected future or recurring execution, provide additional details:
-
For Future execution, enter the Starts at date and time. You also have the option to select the Starts before date and time. If the job cannot start before that time, it will be canceled.
-
For Recurring execution, select the start date and time, frequency, and the condition for ending the recurring job. You can choose the recurrence to never end, end at a certain time, or end after a given number of repetitions. You can also add Purpose - a special label for tracking the job. There can only be one active job with a given purpose at a time.
Click Next after you have entered the required information.
-
-
Review job details. You have the option to return to any part of the job wizard and edit the information.
-
Click Submit to schedule the job for execution.
20.2.5. Executing a remote job by using Hammer CLI
You can execute a job that is based on a job template against one or more hosts.
|
Note
|
Ansible jobs run in batches on multiple hosts, so you cannot cancel a job running on a specific host. A job completes only after the Ansible Playbook runs on all hosts in the batch. |
For more information about creating, monitoring, or canceling remote jobs with Hammer CLI, enter hammer job-template --help and hammer job-invocation --help.
-
Enter the following command on Foreman:
$ hammer settings set \ --name remote_execution_global_proxy \ --value false
-
Find the ID of the job template you want to use:
$ hammer job-template list
-
Show the template details to see parameters required by your template:
$ hammer job-template info --id My_Template_ID
-
Execute a remote job with custom parameters:
$ hammer job-invocation create \ --inputs My_Key_1="My_Value_1",My_Key_2="My_Value_2",... \ --job-template "My_Template_Name" \ --search-query "My_Search_Query"
Replace
My_Search_Querywith the filter expression that defines hosts, for example"name ~ My_Pattern".
20.3. Configuring remote execution
You can configure remote execution in several ways to control how remote jobs run on your hosts. This helps you configure the remote execution process to run in a way that fits your needs.
20.3.1. Configuring the fallback to any Smart Proxy remote execution setting by using Foreman web UI
You can enable the Fallback to Any Smart Proxy setting so that Foreman can use other Smart Proxies assigned to hosts when no remote execution Smart Proxy is found for the host subnets. This is useful for hosts with no subnets or when their subnets use Smart Proxies without remote execution enabled.
If the Fallback to Any Smart Proxy setting is enabled, Foreman adds another set of Smart Proxies to select the remote execution Smart Proxy from. Foreman also selects the most lightly loaded Smart Proxy from the set of all Smart Proxies assigned to the host, such as the following:
-
DHCP, DNS and TFTP Smart Proxies assigned to the subnets of the hosts
-
DNS Smart Proxy assigned to the host domain
-
Realm Smart Proxy assigned to the host realm
-
Puppet server Smart Proxy
-
Puppet CA Smart Proxy
-
OpenSCAP Smart Proxy
-
In the Foreman web UI, navigate to Administer > Settings.
-
Click Remote Execution.
-
Configure the Fallback to Any Smart Proxy setting.
20.3.2. Configuring the fallback to any Smart Proxy remote execution setting by using Hammer CLI
You can enable the Fallback to Any Smart Proxy setting so that Foreman can use other Smart Proxies assigned to hosts when no remote execution Smart Proxy is found for the host subnets. This is useful for hosts with no subnets or when their subnets use Smart Proxies without remote execution enabled.
If the Fallback to Any Smart Proxy setting is enabled, Foreman adds another set of Smart Proxies to select the remote execution Smart Proxy from. Foreman also selects the most lightly loaded Smart Proxy from the set of all Smart Proxies assigned to the host, such as the following:
-
DHCP, DNS and TFTP Smart Proxies assigned to the host’s subnets
-
DNS Smart Proxy assigned to the host’s domain
-
Realm Smart Proxy assigned to the host’s realm
-
Puppet server Smart Proxy
-
Puppet CA Smart Proxy
-
OpenSCAP Smart Proxy
-
Configure the Fallback to Any Smart Proxy setting:
$ hammer settings set \ --name remote_execution_fallback_proxy \ --value true
20.3.3. Configuring the global Smart Proxy remote execution setting by using Foreman web UI
You can enable the Enable Global Smart Proxy setting so that Foreman can use any remote execution Smart Proxy in the organization and location of the host when none is found for the subnets of the host. You can disable it to limit job execution to Smart Proxies assigned to the subnets of the host only.
If the Enable Global Smart Proxy setting is enabled, Foreman adds another set of Smart Proxies to select the remote execution Smart Proxy from. Foreman also selects the most lightly loaded remote execution Smart Proxy from the set of all Smart Proxies in the host’s organization and location to execute a remote job.
-
In the Foreman web UI, navigate to Administer > Settings.
-
Click Remote Execution.
-
Configure the Enable Global Smart Proxy setting.
20.3.4. Configuring the global Smart Proxy remote execution setting by using Hammer CLI
You can enable the Enable Global Smart Proxy setting so that Foreman can use any remote execution Smart Proxy in the organization and location of the host when none is found for the subnets of the host. You can disable it to limit job execution to Smart Proxies assigned to the subnets of the host only.
If the Enable Global Smart Proxy setting is enabled, Foreman adds another set of Smart Proxies to select the remote execution Smart Proxy from. Foreman also selects the most lightly loaded remote execution Smart Proxy from the set of all Smart Proxies in the host’s organization and location to execute a remote job.
-
Enter the
hammer settings setcommand on Foreman to configure theEnable Global Smart Proxysetting. To set the value totrue, enter the following command:$ hammer settings set \ --name remote_execution_global_proxy \ --value true
20.3.5. Setting an alternative directory for remote execution jobs in push mode
By default, Foreman uses the /var/tmp directory on hosts for remote execution jobs in push mode.
You can use foreman-installer to set an alternative directory for executing remote execution jobs in push mode.
If the /var/tmp/ directory on your host is mounted with the noexec flag, Foreman cannot execute remote execution job scripts in this directory.
-
On your host, create a new directory:
# mkdir /My_Remote_Working_Directory
-
Copy the SELinux context from the default
/var/tmpdirectory:# chcon --reference=/var/tmp /My_Remote_Working_Directory
-
Configure your Foreman server or Smart Proxy server to use the new directory:
# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-remote-working-dir /My_Remote_Working_Directory
20.3.6. Setting an alternative directory for remote execution jobs in pull mode
By default, Foreman uses the /run directory on hosts for remote execution jobs in pull mode.
You can use the Yggdrasil service to set an alternative directory for executing remote execution jobs in pull mode.
If the /run/ directory on your host is mounted with the noexec flag, Foreman cannot execute remote execution job scripts in this directory.
-
Determine which version of the
yggdrasilpackage is installed on the host:-
On Enterprise Linux and SUSE Linux Enterprise Server hosts:
$ rpm --query yggdrasil
-
On Debian/Ubuntu hosts:
$ dpkg-query --show yggdrasil-mqtt
-
-
Create a new directory:
# mkdir /My_Remote_Working_Directory
-
Access the Yggdrasil service configuration:
-
If your host has
yggdrasilversion 0.4.z or later installed:# systemctl edit com.redhat.Yggdrasil1.Worker1.foreman
-
If your host has
yggdrasilversion 0.2.z or earlier installed:# systemctl edit yggdrasild
-
-
Specify the alternative directory by adding the following line to the configuration:
Environment=FOREMAN_YGG_WORKER_WORKDIR=/My_Remote_Working_Directory
-
Restart the Yggdrasil services:
-
If your host has
yggdrasilversion 0.4.z or later installed:# systemctl restart yggdrasil com.redhat.Yggdrasil1.Worker1.foreman
-
If your host has
yggdrasilversion 0.2.z or earlier installed:# systemctl restart yggdrasild
-
20.3.7. Altering the privilege elevation method
By default, push-based remote execution uses sudo to switch from the SSH user to the effective user that executes the script on your host.
You can globally configure an alternative method in your Foreman settings.
|
Note
|
If the SSH user and effective user for push-based transport are non-root users, ensure the |
-
Your user account has a role assigned that grants the
view_settingsandedit_settingspermissions. -
If you use
dzdofor Ansible jobs, thecommunity.generalAnsible collection must be installed. This collection contains the required dzdo become plugin. For more information, see Installing collections in Ansible documentation.
-
Navigate to Administer > Settings.
-
Select the Remote Execution tab.
-
Click the value of the Effective User Method setting.
-
Select the new value.
-
Click Submit.
20.3.8. Adding Foreman server SSH key to authorized keys
If you want to run remote execution jobs on Foreman server itself, add the following SSH key to authorized keys on your Foreman server.
-
You can access your Foreman server by using SSH as root.
-
If the
~root/.ssh/authorized_keysfile does not exist, create it with restrictive ownership and permissions:-
If the
~root/.sshdirectory does not exist, create it:# mkdir ~root/.ssh
-
Ensure that the directory is owned by the
rootuser:# chown root:root ~root/.ssh
-
Ensure that the directory is accessible only to the
rootuser:# chmod 700 ~root/.ssh
-
Create the
authorized_keysfile:# touch ~root/.ssh/authorized_keys
-
Ensure that the
authorized_keysfile is owned by therootuser:# chown root:root ~root/.ssh/authorized_keys
-
Ensure that the
authorized_keysfile is accessible only to therootuser:# chmod 600 ~root/.ssh/authorized_keys
-
-
Add the SSH key of the
foreman-proxyuser to theauthorized_keysfile:# cat ~foreman-proxy/.ssh/id_rsa_foreman_proxy.pub >>~root/.ssh/authorized_keys
20.3.9. Distributing SSH keys for remote execution manually
You can distribute SSH keys for remote execution manually.
-
Copy the SSH pub key from your Smart Proxy to your target host:
# ssh-copy-id -i ~foreman-proxy/.ssh/id_rsa_foreman_proxy.pub root@client.example.com
Repeat this step for each target host you want to manage.
-
On your Smart Proxy, confirm that the key was successfully copied to the target host:
# ssh -i ~foreman-proxy/.ssh/id_rsa_foreman_proxy root@client.example.com
20.3.10. Adding a passphrase to SSH key used for remote execution
By default, Smart Proxy uses a non-passphrase protected SSH key to execute remote jobs on hosts. You can protect the SSH key with a passphrase by following this procedure.
-
On your Foreman server or Smart Proxy server, use
ssh-keygento add a passphrase to your SSH key:# ssh-keygen -p -f ~foreman-proxy/.ssh/id_rsa_foreman_proxy
-
Users now must use a passphrase when running remote execution jobs on hosts.
20.3.11. Using the Foreman API to obtain SSH keys for remote execution
You can obtain the Foreman SSH key from Smart Proxy and add it to the authorized_keys on the host so that remote execution jobs can run on the host using SSH.
Use this when you cannot use the standard distribution method, for example in automated or scripted setups.
Perform these steps on each target host where you want to run remote execution jobs.
-
On the target host, create the
~/.sshdirectory to store the SSH key:# mkdir ~/.ssh
-
Download the SSH key from Smart Proxy:
# curl https://smartproxy.example.com:9090/ssh/pubkey >> ~/.ssh/authorized_keys
-
Configure permissions for the
~/.sshdirectory:# chmod 700 ~/.ssh
-
Configure permissions for the
authorized_keysfile:# chmod 600 ~/.ssh/authorized_keys
20.3.12. Configuring a Agama template to distribute SSH keys during provisioning
You can add a remote_execution_ssh_keys snippet to your custom Agama template to deploy SSH keys to hosts during provisioning.
Agama templates that Foreman ships include this snippet by default.
Foreman copies the SSH key for remote execution to the systems during provisioning.
-
To include the public key in newly-provisioned hosts, add the following snippet to the Agama template that you use:
<%= snippet 'remote_execution_ssh_keys' %>
20.3.13. Configuring a Kickstart template to distribute SSH keys during provisioning
You can add a remote_execution_ssh_keys snippet to your custom Kickstart template to deploy SSH keys to hosts during provisioning.
Kickstart templates that Foreman ships include this snippet by default.
Foreman copies the SSH key for remote execution to the systems during provisioning.
-
To include the public key in newly-provisioned hosts, add the following snippet to the Kickstart template that you use:
<%= snippet 'remote_execution_ssh_keys' %>
20.3.14. Configuring a Preseed template to distribute SSH keys during provisioning
You can add a remote_execution_ssh_keys snippet to your custom Preseed template to deploy SSH keys to hosts during provisioning.
Preseed templates that Foreman ships include this snippet by default.
Foreman copies the SSH key for remote execution to the systems during provisioning.
-
To include the public key in newly-provisioned hosts, add the following snippet to the Preseed template that you use:
<%= snippet 'remote_execution_ssh_keys' %>
20.4. Configuring Smart Proxy and hosts to authenticate with SSH certificates during remote execution
By default, Foreman follows the Trust on First Use (TOFU) model when establishing a remote execution connection. You can reconfigure your Smart Proxy to use SSH certificates instead. SSH certificates are signed by a Certificate Authority (CA), which allows centralized trust management and revocation capabilities.
You can configure SSH certificate authentication in the following ways. You can configure one or both of these authentication methods depending on your security requirements:
- Using user certificates
-
When your Smart Proxy connects to hosts, it presents a signed certificate. Hosts trust the CA that signed the certificate, eliminating the need to distribute individual SSH public keys to each host.
- Using host certificates
-
When your Smart Proxy connects to hosts, the hosts present signed certificates. Smart Proxy verifies that it is connecting to legitimate hosts, helping prevent man-in-the-middle attacks.
If you configure Smart Proxy to use SSH certificates, the configuration will apply to running Ansible jobs as well.
20.4.1. Enabling SSH certificate authentication on Smart Proxy
You can configure Smart Proxy to present an SSH certificate signed by a Certificate Authority (CA) to hosts instead of a plain SSH public key.
|
Warning
|
After enabling this feature, SSH certificate authentication works on all newly registered or provisioned hosts. Existing hosts will continue to trust plain SSH keys of your Smart Proxy until you configure those hosts to trust the CA. To configure existing hosts to accept the SSH certificate from your Smart Proxy, complete Configuring registered hosts to accept an SSH certificate from Smart Proxy. |
-
You have a CA for signing SSH certificates.
-
On the Smart Proxy server, locate the SSH key pair that Smart Proxy uses for remote execution. You can find the private key location in
/etc/foreman-proxy/settings.d/remote_execution_ssh.ymlunder the:ssh_identity_key_file:setting. By default, the location is/var/lib/foreman-proxy/ssh/id_rsa_foreman_proxy. -
If the CA is on a different server than your Smart Proxy server, copy the public key file of the Smart Proxy to the CA server.
-
Sign the Smart Proxy SSH public key with your CA.
NoteThe
ssh-keygencommand creates the certificate file with the nameMy_Smart_Proxy_Private_Key-cert.pub. Do not change the name of the file. By default, the created SSH certificate is namedid_rsa_foreman_proxy-cert.pub. -
If the CA is on a different server than your Smart Proxy server, ensure the Smart Proxy server has the SSH certificate and the CA public key file:
-
Copy the created SSH certificate file back to the Smart Proxy server into the same directory as the original SSH key pair.
-
Copy the CA public key file to the Smart Proxy server.
NoteBy default, the
foreman-proxyuser has read access to the CA public key file. Do not store the file in non-standard directories so that theforeman-proxyuser can read the file. Foreman community recommends storing the file in the/etc/ssh/directory.
-
-
Enable SSH certificate authentication on your Smart Proxy:
# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-ssh-user-ca-public-key-file My_CA_Public_Key_File_Path
-
Run a remote execution job on a host through your Smart Proxy with SSH certificate authentication enabled.
-
On the host, view the
sshdlogs:# journalctl -u sshd
-
Find the log message that confirms that the SSH certificate was used for authentication:
Accepted publickey for <SSH USER> from <IP> port 22 ssh2: RSA-CERT ID foreman-proxy CA RSA
20.4.2. Disabling SSH certificate authentication on Smart Proxy
If you disable SSH certificate authentication on Smart Proxy, you will revert to plain SSH key pair authentication.
-
Distribute your Smart Proxy SSH keys to the hosts that use your Smart Proxy for remote execution. For more information, see Distributing SSH keys for remote execution.
-
Delete the SSH certificate file of the Smart Proxy. By default, the path of this file is
/var/lib/foreman-proxy/ssh/id_rsa_foreman_proxy-cert.pub. -
Disable the SSH certificate authentication:
# foreman-installer \ --reset-foreman-proxy-plugin-remote-execution-script-ssh-user-ca-public-key-file
20.4.3. Rotating Smart Proxy SSH certificate
You can rotate the SSH certificate used by Smart Proxy for remote execution by generating a new SSH key pair and having it signed by your configured CA. For example, this is useful if the SSH certificate used by Smart Proxy for remote execution is no longer valid.
-
You have SSH certificate authentication enabled on Smart Proxy.
-
You have a configured CA for signing SSH certificates.
-
On the Smart Proxy server, locate the directory that Smart Proxy uses for remote execution by checking where the configured Smart Proxy SSH private key is stored. You can find the location of the SSH private key in
/etc/foreman-proxy/settings.d/remote_execution_ssh.ymlunder the:ssh_identity_key_file:setting. By default, the directory is/var/lib/foreman-proxy/ssh/. -
On the Smart Proxy server, generate a new SSH key pair in the directory:
# ssh-keygen -f My_Smart_Proxy_SSH_Directory/My_New_SSH_Key
-
Set the correct ownership for the new key files:
# chown foreman-proxy:foreman-proxy My_Smart_Proxy_SSH_Directory/My_New_SSH_Key*
-
If the CA is on a different server than your Smart Proxy server, copy the new public key file to the CA server.
-
Sign the new SSH public key with your CA.
-
If the CA is on a different server than your Smart Proxy server, copy the created SSH certificate file back to the Smart Proxy server into the Smart Proxy SSH directory.
-
Set the correct ownership for the certificate file:
# chown foreman-proxy:foreman-proxy My_Smart_Proxy_SSH_Directory/My_New_SSH_Key-cert.pub
-
Configure Smart Proxy to use the new SSH key:
# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-ssh-identity-file My_Smart_Proxy_SSH_Directory/My_New_SSH_Key
NoteIf you created the new SSH key pair with the same name as the old one and thus replaced the old key pair, you do not need to update your Smart Proxy configuration with foreman-installer.
-
Optional: Remove the old SSH key files from the Smart Proxy SSH directory.
-
Run a remote execution job on a host through your Smart Proxy with SSH certificate authentication enabled.
-
On the host, view the
sshdlogs:# journalctl -u sshd
-
Find the log message that confirms that the SSH certificate was used for authentication:
Accepted publickey for <SSH USER> from <IP> port 22 ssh2: RSA-CERT ID foreman-proxy CA RSA
20.4.4. Configuring registered hosts to accept an SSH certificate from Smart Proxy
After you enable SSH certificate authentication on your Smart Proxy, you can configure hosts to accept SSH certificates from your Smart Proxy. This ensures the hosts will no longer accept plain SSH keys during a remote execution connection.
You can use remote execution to apply these changes.
Perform these steps on each host that uses your Smart Proxy for remote execution and was registered before you enabled SSH certificate authentication on your Smart Proxy.
-
You have a Certificate Authority (CA) for signing SSH certificates.
-
Copy the CA public key file to the host.
-
Ensure that the
/etc/ssh/sshd_config.d/directory exists:# mkdir --parents /etc/ssh/sshd_config.d/
-
Configure the
sshdservice to trust the CA:# echo 'TrustedUserCAKeys My_CA_Public_Key_File_Path' > /etc/ssh/sshd_config.d/60-foreman-user-ca.conf
-
Set the correct SELinux context for the created file:
# restorecon /etc/ssh/sshd_config.d/60-foreman-user-ca.conf
-
Restart the
sshdservice:# systemctl restart sshd
-
Remove existing SSH keys of the Smart Proxy from the
authorized_keysfile of your SSH user. By default, the SSH user is root and the SSH keys are associated with theforeman-proxyuser:# sed -i '/foreman-proxy/d' ~/.ssh/authorized_keys
NoteThis command might not work if you configured custom SSH keys on your Smart Proxy. In that case, manually edit the
authorized_keysfile.
20.4.5. Enabling SSH host certificate verification on Smart Proxy
Your Smart Proxy can use SSH host certificates to verify the identity of hosts. In this configuration, Smart Proxy verifies that hosts present valid certificates signed by a trusted Certificate Authority (CA) during SSH connections. Your Smart Proxy can trust host certificates signed by multiple CAs.
|
Important
|
After you enable host certificate verification on Smart Proxy, all hosts that use this Smart Proxy for remote execution can authenticate only if they are configured to use host certificates. |
-
You have a CA for signing SSH host certificates.
-
On each host that uses this Smart Proxy for remote execution, prepare the SSH certificate for the host:
-
Copy one of the public key files of the host to the CA server. The public keys are located in
/etc/ssh/. -
Sign the public key with your CA to create an SSH host certificate. Use the
-hoption when generating the SSH host certificate withssh-keygen.ImportantThe
ssh-keygencommand creates the certificate file with the nameMy_Host_Private_SSH_Key-cert.pub. Do not change the name of the file. -
Copy the SSH certificate file back to the host. The location must be the same as the location of the private key.
-
Configure the host to use the certificate:
# mkdir --parents /etc/ssh/sshd_config.d/ # echo 'HostCertificate My_Host_SSH_Certificate_Path' > /etc/ssh/sshd_config.d/60-host-cert.conf # restorecon -R /etc/ssh/
NoteIf the host SSH public key you used for the certificate is not one of the default keys (
/etc/ssh/ssh_host_ecdsa_key.pub,/etc/ssh/ssh_host_ed25519_key.pub, or/etc/ssh/ssh_host_rsa_key.pub), also add the host key configuration:# echo 'HostKey My_Host_Private_SSH_Key_Path' >> /etc/ssh/sshd_config.d/60-host-cert.conf
-
Restart the
sshdservice:# systemctl restart sshd
-
-
On the Smart Proxy, configure host certificate verification:
-
If the host CA is not located on the Smart Proxy server, copy the host CA public key file to your Smart Proxy server. If you have multiple host CAs, place all of their public keys in a single file, with each key on a separate line.
-
Enable host certificate verification:
# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-ssh-host-ca-public-keys-file My_Host_CA_Public_Keys_File_Path
-
-
Run a remote execution job on a host that is not configured with a host certificate signed by a trusted CA. The attempt results in an authentication failure.
20.4.6. Disabling SSH host certificate verification on Smart Proxy
If you disable SSH host certificate verification on Smart Proxy, you will revert to the Trust On First Use (TOFU) model.
-
On Smart Proxy, disable SSH host certificate verification:
# foreman-installer \ --reset-foreman-proxy-plugin-remote-execution-script-ssh-host-ca-public-keys-file
20.5. Tuning authentication and performance for remote execution
Foreman supports advanced authentication methods and performance tuning for remote execution. You can configure Kerberos-based authentication and control job execution rates on Smart Proxies.
20.5.1. Configuring a keytab for Kerberos ticket granting tickets
You can configure Foreman to use a keytab so that it obtains Kerberos ticket-granting tickets (TGTs) automatically for remote execution. This avoids manually retrieving tickets and enables remote jobs to use Kerberos authentication.
-
Find the ID of the
foreman-proxyuser:# id -u foreman-proxy
-
Modify the
umaskvalue so that new files have the permissions600:# umask 077
-
Create the directory for the keytab:
# mkdir -p "/var/kerberos/krb5/user/My_User_ID"
-
Create a keytab or copy an existing keytab to the directory:
# cp My_Client.keytab /var/kerberos/krb5/user/My_User_ID/client.keytab
-
Change the directory owner to the
foreman-proxyuser:# chown -R foreman-proxy:foreman-proxy "/var/kerberos/krb5/user/My_User_ID"
-
Ensure that the keytab file is read-only:
# chmod -wx "/var/kerberos/krb5/user/My_User_ID/client.keytab"
-
Restore the SELinux context:
# restorecon -RvF /var/kerberos/krb5
20.5.2. Configuring Kerberos authentication for remote execution
You can use Kerberos authentication to establish an SSH connection for remote execution on Foreman hosts.
-
Enroll Foreman server on the Kerberos server
-
Enroll the Foreman target host on the Kerberos server
-
Configure and initialize a Kerberos user account for remote execution
-
Ensure that the
foreman-proxyuser on Foreman has a valid Kerberos ticket-granting ticket (TGT)
-
Enable Kerberos authentication for remote execution:
# foreman-installer --foreman-proxy-plugin-remote-execution-script-ssh-kerberos-auth true
-
To edit the default user for remote execution, in the Foreman web UI, navigate to Administer > Settings and click the Remote Execution tab. In the SSH User row, edit the second column and add the user name for the Kerberos account.
-
Navigate to remote_execution_effective_user and edit the second column to add the user name for the Kerberos account.
-
To confirm that Kerberos authentication is ready to use, run a remote job on the host. For more information, see Configuring and setting up remote jobs.
20.5.3. Setting the job rate limit on Smart Proxy
You can limit the maximum number of active jobs on a Smart Proxy at a time to prevent performance spikes.
The job is active from the time Smart Proxy first tries to notify the host about the job until the job is finished on the host.
The job rate limit only applies to mqtt based jobs.
|
Note
|
The optimal maximum number of active jobs depends on the computing resources of your Smart Proxy server. By default, the maximum number of active jobs is unlimited. |
-
Set the maximum number of active jobs using
foreman-installer:# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-mqtt-rate-limit MAX_JOBS_NUMBER
For example:
# foreman-installer \ --foreman-proxy-plugin-remote-execution-script-mqtt-rate-limit 200
20.6. Customizing remote jobs
You can customize remote jobs in Foreman to fit your needs. For example, you can create and customize job templates or you can import Ansible playbooks to use in your remote jobs.
20.6.1. Creating a job template by using Foreman web UI
You can create a job template from the Foreman web UI to define a reusable script or Ansible task that you can run on hosts via remote execution.
-
In the Foreman web UI, navigate to Hosts > Templates > Job templates.
-
Click New Job Template.
-
Click the Template tab, and in the Name field, enter a unique name for your job template.
-
Select Default to make the template available for all organizations and locations.
-
Create the template directly in the template editor or upload it from a text file by clicking Import.
-
Optional: In the Audit Comment field, add information about the change.
-
Click the Job tab, and in the Job category field, enter your own category or select from the default categories.
-
Optional: In the Description Format field, enter a description template. For example,
Install package %{package_name}. You can also use%{template_name}and%{job_category}in your template. -
From the Provider Type list, select SSH for shell scripts and Ansible for Ansible tasks or playbooks.
-
Optional: In the Timeout to kill field, enter a timeout value to terminate the job if it does not complete.
-
Optional: Click Add Input to define an input parameter. Parameters are requested when executing the job and do not have to be defined in the template. For examples, see the Help tab.
-
Optional: Click Foreign input set to include other templates in this job.
-
Optional: In the Effective user area, configure a user if the command cannot use the default
remote_execution_effective_usersetting. -
Optional: If this template is a snippet to be included in other templates, click the Type tab and select Snippet.
-
Optional: If you use the Ansible provider, click the Ansible tab.
-
Select Enable Ansible Callback to allow hosts to send facts, which are used to create configuration reports, back to Foreman after a job finishes.
-
Select Enable Ansible Check Mode to run jobs based on the template in Ansible check mode, which executes Ansible playbooks without making changes to hosts. For more information on Ansible check mode, see Validating tasks: check mode and diff mode in Ansible Documentation.
-
-
Click the Location tab and add the locations where you want to use the template.
-
Click the Organizations tab and add the organizations where you want to use the template.
-
Click Submit to save your changes.
20.6.2. Creating a job template by using Hammer CLI
You can create a job template by using Hammer CLI to define a reusable script or Ansible task that you can run on hosts via remote execution.
-
Create a job template using a template-definition file:
$ hammer job-template create \ --file "Path_to_My_Template_File" \ --job-category "My_Category_Name" \ --name "My_Template_Name" \ --provider-type SSH
20.6.3. Importing an Ansible Playbook by name
You can import Ansible Playbooks by name to Foreman from collections installed on Smart Proxy. Foreman creates a job template from each playbook so you can run it on hosts via remote execution without writing the template manually.
When you import an Ansible Playbook, Foreman creates a job template from the imported playbook and places the template in the Ansible Playbook - Imported job category.
If you have a custom collection, place it in /etc/ansible/collections/ansible_collections/My_Namespace/My_Collection.
-
Ansible plugin is enabled.
-
Your Foreman account has a role that grants the
import_ansible_playbookspermission.
-
Fetch the available Ansible Playbooks by using the following API request:
$ curl \ --header 'Content-Type: application/json' \ --request GET \ https://foreman.example.com/ansible/api/v2/ansible_playbooks/fetch?proxy_id=My_Smart_Proxy_ID
-
Select the Ansible Playbook you want to import and note its name.
-
Import the Ansible Playbook by its name:
$ curl \ --data '{ "playbook_names": ["My_Playbook_Name"] }' \ --header 'Content-Type: application/json' \ --request PUT \ https://foreman.example.com/ansible/api/v2/ansible_playbooks/sync?proxy_id=My_Smart_Proxy_IDYou get a notification in the Foreman web UI after the import completes.
-
You can run the playbook by executing a remote job from the created job template. For more information, see Configuring and setting up remote jobs.
20.6.4. Importing all available Ansible Playbooks
When Ansible collections on your Smart Proxy hold playbooks you want to run from Foreman, you can import all available Ansible Playbooks to Foreman in one step.
When you import an Ansible Playbook, Foreman creates job templates from the imported playbooks and places the templates in the Ansible Playbook - Imported job category.
If you have a custom collection, place it in /etc/ansible/collections/ansible_collections/My_Namespace/My_Collection.
-
Ansible plugin is enabled.
-
Your Foreman account has a role that grants the
import_ansible_playbookspermission.
-
Import the Ansible Playbooks by using the following API request:
# curl -X PUT -H 'Content-Type: application/json' https://foreman.example.com/ansible/api/v2/ansible_playbooks/sync?proxy_id=My_Smart_Proxy_ID
You get a notification in the Foreman web UI after the import completes.
-
You can run the playbooks by executing a remote job from the created job templates. For more information, see Configuring and setting up remote jobs.
20.6.5. Customizing job templates
Foreman provides default job templates that you can use for executing jobs. Default job templates are locked for editing but you can clone them and edit the clone.
Job templates use the Embedded Ruby (ERB) syntax. Ansible job templates use YAML syntax.
At run time, job templates can accept parameter variables that you define for a host. Note that only the parameters visible on the Parameters tab at the host’s edit page can be used as input parameters for job templates.
-
In the Foreman web UI, navigate to Hosts > Templates > Job templates.
-
To clone a template, in the Actions column, select Clone.
-
Enter a unique name for the clone and click Submit to save the changes.
-
In the list of job templates, click the cloned template to start editing it.
NoteAn Ansible template must begin with
---. You can embed an Ansible Playbook YAML file into the job template body. You can also add ERB syntax to customize your YAML Ansible template.
20.6.6. Scheduling a recurring Ansible job for a host
You can schedule a recurring Ansible job to run on a host at a set interval. This is useful for regular tasks such as compliance checks, patching, or configuration drift remediation.
-
Your user account has the
view_foreman_tasks,view_job_invocations, andview_recurring_logicspermissions. -
At least one Ansible role is assigned to your host.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select your host.
-
On the Ansible tab, select Jobs.
-
Click Schedule recurring job.
-
In the Repeat list, select the interval.
-
In the Start time field, enter the start time of the recurring job.
-
In the Start date field, enter the start date of the recurring job.
-
Click Submit.
20.6.7. Scheduling a recurring Ansible job for a host group
You can schedule a recurring Ansible job to run on a host group at a set interval. This is useful for regular tasks such as compliance checks, patching, or configuration drift remediation across all hosts that are assigned to this host group.
-
At least one Ansible role is assigned to your host group.
-
At least one host is assigned to your host group.
-
In the Foreman web UI, navigate to Configure > Host Groups.
-
In the Actions column, select Configure Ansible Job for the host group you want to schedule an Ansible roles run for.
-
Click Schedule recurring job.
-
In the Repeat list, select the interval.
-
In the Start time field, enter the start time of the recurring job.
-
In the Start date field, enter the start date of the recurring job.
-
Click Submit.
20.6.8. Using Ansible provider for package and errata actions
By default, Foreman is configured to use the Script provider templates for remote execution jobs. If you prefer using Ansible job templates for your remote jobs, you can configure Foreman to use them by default for remote execution features associated with them.
|
Note
|
Remember that Ansible job templates only work when remote execution is configured for |
-
In the Foreman web UI, navigate to Administer > Remote Execution Features.
-
Find each feature whose name contains
by_search. -
Change the job template for these features from
Katello Script DefaulttoKatello Ansible Default. -
Click Submit.
Foreman now uses Ansible provider templates for remote execution jobs by which you can perform package and errata actions. This applies to job invocations from the Foreman web UI as well as by using
hammer job-invocation createwith the same remote execution features that you have changed.
20.7. Remote execution reference
Remote execution in Foreman provides advanced configuration options and extended scheduling capabilities for running jobs on hosts.
20.7.1. Advanced settings in the job wizard
Some job templates require you to enter advanced settings. Some of the advanced settings are only visible to certain job templates. Below is the list of general advanced settings.
- SSH user
-
A user to be used for connecting to the host through SSH.
- Effective user
-
A user to be used for executing the job. By default it is the SSH user. If it differs from the SSH user, su or sudo, depending on your settings, is used to switch the accounts.
-
If you set an effective user in the advanced settings, Ansible sets
ansible_become_userto your input value andansible_becometotrue. This means that if you use the parametersbecome: trueandbecome_user: My_Userwithin a playbook, these will be overwritten by Foreman. -
If your SSH user and effective user are identical, Foreman does not overwrite the
become_user. Therefore, you can set a custombecome_userin your Ansible Playbook.
-
- Description
-
A description template for the job.
- Timeout to kill
-
Time in seconds from the start of the job after which the job should be killed if it is not finished already.
- Time to pickup
-
Time in seconds after which the job is canceled if it is not picked up by a client. This setting only applies to hosts using
pull-mqtttransport. - Password
-
Is used if SSH authentication method is a password instead of the SSH key.
- Private key passphrase
-
Is used if SSH keys are protected by a passphrase.
- Effective user password
-
Is used if effective user is different from the ssh user.
- Concurrency level
-
Defines the maximum number of jobs executed at once. This can prevent overload of system resources in a case of executing the job on a large number of hosts.
- Execution ordering
-
Determines the order in which the job is executed on hosts. It can be alphabetical or randomized.
20.7.2. Extended cron line syntax in remote jobs
When scheduling a cron job with remote execution, you can use an extended cron line to specify the cadence of the job. Extended cron syntax adds patterns on top of the standard five-field cron line when you schedule remote execution jobs.
The standard cron line has five fields: minute, hour, day of the month, month, and day of the week.
For example, 0 5 * * * means every day at 5 AM.
For more information about the standard cron line, see crontab guru.
Extended syntax supports the following patterns:
#to specify a concrete weekday in a month-
For example:
-
0 0 * * mon#1specifies first Monday of the month -
0 0 * * fri#3,fri#4specifies third and fourth Fridays of the month -
0 7 * * fri#-1specifies the last Friday of the month at 07:00 -
0 7 * * fri#Lalso specifies the last Friday of the month at 07:00 -
0 23 * * mon#2,tuespecifies the second Monday of the month and every Tuesday, at 23:00
-
%to specify every n-th day of the month-
For example:
-
9 0 * * sun%2specifies every other Sunday at 00:09 -
0 0 * * sun%2+1specifies every odd Sunday -
9 0 * * sun%2,tue%3specifies every other Sunday and every third Tuesday
-
&to specify that the day of month must match day of week-
For example:
-
0 0 30 * 1&specifies the 30th day of the month, but only if it is Monday
-
21. Managing packages in Foreman
You can use Foreman to install, upgrade, and remove packages and to enable or disable repositories on hosts. Package actions use remote execution so you can manage software on hosts from a central place.
21.1. Enabling and disabling repositories on hosts
You can enable or disable repositories on a host from the Foreman web UI to control which package sources the host can use. This affects which packages are available for installation or upgrade on the host.
-
In the Foreman web UI, navigate to Hosts > All Hosts,
-
Select a host.
-
On the Content tab, click the Repository sets tab.
-
Click the vertical ellipsis to choose Override to disabled or Override to enabled to disable or enable repositories on hosts.
21.2. Installing packages on a host
You can review and install packages on a host from the Foreman web UI so that the host has the software it needs. Available packages depend on the content view environments assigned to the host.
-
The host is assigned to a content view and lifecycle environment.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select a host.
-
On the Content tab, click the Packages tab.
-
On the vertical ellipsis icon next to the upgrade button, click Install packages.
-
In the Install packages window, select the package or packages that you want to install on the host.
-
Click Install. The Foreman web UI shows a notification for the remote execution job.
21.3. Upgrading packages on a host
You can upgrade packages on a host in bulk from the Foreman web UI.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select a host.
-
On the Content tab, click the Packages tab.
-
Select Upgradable from the Status list.
-
In the Upgradable to column, select the package version that you want to upgrade to.
-
Select the packages you want to upgrade.
-
Click Upgrade. The Foreman web UI shows a notification for the remote execution job.
21.4. Removing packages from a host
You can remove packages from a host from the Foreman web UI to uninstall software or resolve dependency conflicts.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Select a host.
-
On the Content tab, click the Packages tab.
-
Click the vertical ellipsis for the package you want to remove.
-
Select Remove. The Foreman web UI shows a notification for the remote execution job.
21.5. Managing packages on a host by using API
You can install, upgrade, or remove packages on a host by using the Foreman API for automation, scripts, or integration with other tools.
The example below uses the katello_package_install action to install a package.
You can also use package actions katello_package_upgrade to upgrade or katello_package_remove to remove packages.
-
Specify the API request body in the JSON format. For example:
{ "job_invocation" : { "concurrency_control" : { "concurrency_level" : 100 }, "feature" : "katello_package_install", "inputs" : { "package" : "nano vim" }, "scheduling" : { "start_at" : "2023-09-21T19:00:00+00:00", "start_before" : "2023-09-23T00:00:00+00:00" }, "search_query" : "*", "ssh" : { "effective_user" : "My_Username", "effective_user_password" : "My_Password" }, "targeting_type" : "dynamic_query" } }The example uses the following notable values:
- "job_invocation"
-
Specifies the object which contains the API request.
- "concurrency_level"
-
Optional. Limits the number of hosts on which the job is run concurrently.
- "feature"
-
Specifies the action to be performed. Use
"katello_package_install"to install a package,"katello_package_upgrade"to upgrade a package, or"katello_package_remove"to remove a package. - "package"
-
Specifies the packages on which the action is performed. Separate multiple packages with a whitespace.
- "scheduling"
-
Optional. Specifies time boundaries for when to start the package action.
-
You can specify one or both boundaries in the ISO 8601 format.
-
The action is canceled if it is not possible to perform the package action by this time.
-
If you omit time, it defaults to 00:00:00.
-
If you omit time zone, it defaults to UTC.
-
- "search_query"
-
Specifies the search query that selects the hosts on which you want to perform the package action.
- "ssh"
-
Optional. Specifies the credentials of an SSH user, if you want to perform the package action as that user.
- "dynamic_query"
-
Optional. If you supplied the
"scheduling"object, you can make the search query be evaluated when the job runs by specifying the"targeting_type/dynamic_query"field.-
This is useful if you expect the query to produce a different result at the time of the job run.
-
If you omit this field, it defaults to
"static_query".
-
-
Send a
POSTrequest with the created body to the/api/job_invocationsendpoint of your Foreman server and see a formatted response. For example:$ curl https://foreman.example.com/api/job_invocations \ -H "content-type: application/json" \ -X POST \ -d @Path_To_My_API_Request_Body \ -u My_Username:My_Password \ | python3 -m json.tool
-
In the Foreman web UI, navigate to Monitor > Jobs and see the report of the scheduled or completed remote execution job to perform the package action on the selected hosts.
22. Package mode and image mode hosts
Image mode simplifies enterprise operations by enabling development, operations, and solution providers to use the same container-native tools and techniques to manage both applications and the underlying operating system. Foreman supports image mode for Enterprise Linux hosts in addition to package mode.
22.1. Overview of image mode for hosts
Foreman identifies an image mode host as any system that reports a container image from its bootc status through Subscription Manager. It classifies all other hosts as package mode hosts.
In image mode, users can install and manage packages, but with limitations.
Job templates run the bootc usr-overlay command or use the dnf --transient flag to ensure that packages are installed correctly.
Any packages installed on image mode hosts are temporary and disappear after a reboot.
Because of this, installing packages is generally discouraged, except for debugging purposes or, in some cases, when applying critical security patches.
If you need new packages on an image mode host, consider building a new container image the includes the necessary packages.
After upgrading the image mode host to this image, the new packages will be installed permanently.
On the All Hosts page, you can display the Type column, which includes a mode indicator. This column is disabled by default.
Image mode hosts include additional fields that reflect their boot status. These fields track the container images used in various scenarios:
-
Booted Image & Digest: Indicates the container image the host is currently using.
-
Staged Image & Digest: Indicates the container image the host uses after the next reboot.
-
Available Image & Digest: Represents the container image cached by running
bootc upgrade --check. -
Rollback Image & Digest: Represents the container image the host reverts to after the next reboot if
Bootc rollbackis applied.
22.2. Viewing booted container images by using Foreman web UI
These actions streamline the management of image mode hosts, providing flexibility and control over host operations through Foreman.
-
In the Foreman web UI, navigate to Content > Container Images.
-
Select the Booted tab to view all images used by image mode hosts. This tab displays the spread of digests under specific image paths. More digests under an image path indicate greater drift in the host ecosystem, ideally minimized by ensuring all hosts run the most up-to-date image version.
-
Click the host count to navigate to the All Hosts page, which identifies the hosts associated with each specific image and displays the number of hosts using each digest.
-
Select a host and on the Details tab, locate the Image mode details card to see the current
bootcstatus. -
Click the link to the Bootc Action - Script Default remote execution job in this card to perform a Bootc action on the host. For pull-mode remote execution, the
foreman_ygg_workerpackage must be included in the container image of the image mode hosts.
22.3. Viewing booted container images by using Hammer CLI
These actions streamline the management of image mode hosts, providing flexibility and control over host operations through Foreman.
-
Run the
hammer host bootc imagescommand.
22.4. Package persistence on image mode hosts
Packages installed on an image mode host after image creation are installed with transient package persistence. Transient packages are temporary and are lost after a reboot.
You can view the persistence of installed packages on an image mode host by navigating to the host details in the Foreman web UI, selecting Content > Packages, and checking the Persistence column.
In Hammer CLI, you can view the persistence by running hammer host package list --host-id My_Host_ID --fields ALL.
To persist packages on an image mode host, you can build a new container image that includes the necessary packages. After upgrading the image mode host to the new image, the new packages are installed permanently on the host.
22.5. Persisting transient packages in your image
You can generate a Containerfile install command using the transient packages on your image mode host. Then, you can use this command to rebuild your image to make the packages persistent.
22.5.1. Generating a Containerfile command by using Foreman web UI
You can generate a Containerfile install command by using Foreman web UI to persist transient packages in your container image.
-
Your Foreman account has a role that grants the
view_hostspermission.
-
In the Foreman web UI, navigate to Hosts > All Hosts.
-
Click the name of a host.
-
Select the Content tab.
-
Select the Packages tab.
-
Select the packages you want to include in the command.
-
Click the package table menu icon.
-
Select Generate containerfile install command.
-
If Foreman does not recognize persistence for any of the selected packages and you want to include them in the command, enable Include packages with unknown persistence.
-
Click Copy to copy the command to your clipboard.
-
Include the generated command in your Containerfile and rebuild the image.
22.5.2. Generating a Containerfile command by using Hammer CLI
You can generate a Containerfile install command by using Hammer CLI to persist transient packages in your container image.
-
Your Foreman account has a role that grants the
view_hostspermission.
-
Generate the Containerfile command:
$ hammer host package containerfile-install-command --host-id My_Host_ID
-
Copy the generated command from the output.
-
Include the generated command in your Containerfile and rebuild the image.
22.5.3. Generating a Containerfile command by using Foreman API
You can generate a Containerfile install command by using Foreman API to persist transient packages in your container image.
-
Your Foreman account has a role that grants the
view_hostspermission.
-
Send a
GETrequest to the/api/hosts/:host_id/transient_packages/containerfile_install_commandendpoint. -
Copy the generated command from the response.
-
Include the generated command in your Containerfile and rebuild the image.
22.6. Remote execution jobs for image mode hosts
You can use the remote execution jobs under the Bootc job category to manage image mode hosts:
-
Bootc Action - Script Default: Select any Bootc action from the dropdown menu, enter arguments, and specify a target.
-
Bootc Rollback - Script Default: Run Bootc rollback to revert to a previous image.
-
Bootc Status - Script Default: Run Bootc status with optional extra parameters to check the status.
-
Bootc Switch - Script Default: Run Bootc switch with a mandatory image input and optional extra parameters to switch to a different image.
-
Bootc Upgrade - Script Default: Run Bootc upgrade with optional extra parameters to update the image.
For pull-mode remote execution, the foreman_ygg_worker package must be included in the container image of the image mode hosts.
Appendix A: Troubleshooting: Remote jobs timing out after yggdrasil update
On hosts that have weak dependencies disabled and are configured to use the yggdrasil pull client, remote jobs can start failing due to timeouts after the yggdrasil package has been updated to version 0.4.z or later.
You can manually install the foreman_ygg_migration package to address the problem.
The pull-based transport configuration relies on the Yggdrasil service and differs based on the version of the yggdrasil package that is installed on the host.
For pull-based remote execution mode to work correctly after yggdrasil version 0.4.z is installed on the host, the Yggdrasil client configuration must be updated.
Installing the foreman_ygg_migration package on the host ensures that Foreman applies the required changes to Yggdrasil configuration.
On hosts with weak dependencies enabled, Foreman automatically installs the foreman_ygg_migration package.
No further steps are required.
On hosts with weak dependencies disabled, you must install the foreman_ygg_migration package manually.
-
Determine which version of the
yggdrasilpackage is installed on the host:$ rpm --query yggdrasil
-
If your host has
yggdrasilversion 0.4.z or later installed, theyggdrasilandcom.redhat.Yggdrasil1.Worker1.foremanservices are expected to be running. Check the status of these services:# systemctl status yggdrasil com.redhat.Yggdrasil1.Worker1.foreman
If the above services are not running, it means that Yggdrasil might not be configured correctly.
-
Install the
foreman_ygg_migrationpackage manually:# dnf install foreman_ygg_migration
Installing
foreman_ygg_migrationensures that Foreman applies the required Yggdrasil configuration changes and enables remote execution in pull mode to work as expected.
-
Check the status of the Yggdrasil services again:
# systemctl status yggdrasil com.redhat.Yggdrasil1.Worker1.foreman
These services should now be running.
Appendix B: Template writing reference
Embedded Ruby (ERB) is a tool for generating text files based on templates that combine plain text with Ruby code. You can use the following Foreman-specific macros and variables in your ERB templates.
Template rendering and ERB context
You can review how Foreman renders ERB templates during provisioning and remote jobs, why safemode is enabled by default, and which features use ERB syntax.
When you provision a host or run a remote job, the code in the ERB runs and variables are replaced with host-specific values. This process is called rendering. Foreman server enables the safemode rendering option by default so harmful template code cannot execute.
Note that the default templates provided by Foreman (Hosts > Templates > Provisioning Templates, Hosts > Templates > Job templates, Monitor > Reports > Report Templates ) also provide a good source of ERB syntax examples.
Foreman uses ERB syntax in the following cases:
- Provisioning templates
-
For more information, see Creating provisioning templates in Foreman web UI in Provisioning hosts.
- Remote execution job templates
-
For more information, see Configuring and setting up remote jobs.
- Report templates
-
For more information, see Using report templates to monitor hosts.
- Templates for partition tables
-
For more information, see Creating partition tables by using Foreman web UI in Provisioning hosts.
- Smart Class Parameters
-
For more information, see Configuring Puppet smart class parameters in Configuring hosts by using Puppet.
Accessing the template writing reference in the Foreman web UI
You can open the template writing reference from the Foreman web UI to look up ERB macros, variables, and syntax when writing or editing provisioning templates, job templates, or report templates.
-
Log in to the Foreman web UI.
-
In the Foreman web UI, navigate to Administer > About.
-
Click the Templates DSL link in the Support section.
Using autocompletion in templates
You can access a list of available macros and usage information in the template editor with the autocompletion option. This works for all templates within Foreman.
-
In the Foreman web UI, navigate to either Hosts > Templates > Partition tables, Hosts > Templates > Provisioning Templates, or Hosts > Templates > Job templates.
-
Click the settings icon at the top right corner of the template editor and select Autocompletion.
-
Press
Ctrl+Spacein the template editor to access a list of all available macros. You can narrow down the list of macros by typing in more information about what you are looking for. For example, if you are looking for a method to list the ID of the content source for a host, you can typehostand check the list of available macros for content source. -
A window next to the dropdown provides a description of the macro, its usage, and the value it will return.
-
When you find the method you are looking for, hit
Enterto input the method.You can also enable Live Autocompletion in the settings menu to view a list of macros that match the pattern whenever you type something. However, this might input macros in unintended places, like package names in a provisioning template.
Writing ERB templates
You can use the following common tags in your ERB templates.
|
Note
|
Because of the varying lengths of the ERB tags, indenting the ERB syntax might seem messy. ERB syntax ignores white space. One method of handling the indentation is to declare the ERB tag at the beginning of each new line and then use white space within the ERB tag to outline the relationships within the syntax, for example: <%- load_hosts.each do |host| -%> <%- if host.build? %> <%= host.name %> build is in progress <%- end %> <%- end %> |
- <% %>
-
All Ruby code is enclosed within
<% %>in an ERB template. The code is executed when the template is rendered. It can contain Ruby control flow structures as well as Foreman-specific macros and variables. For example:<% if @host.operatingsystem.family == "Redhat" && @host.operatingsystem.major.to_i > 6 -%> systemctl <%= input("action") %> <%= input("service") %> <% else -%> service <%= input("service") %> <%= input("action") %> <% end -%>Note that this template silently performs an action with a service and returns nothing at the output.
- <%= %>
-
This provides the same functionality as
<% %>but when the template is executed, the code output is inserted into the template. This is useful for variable substitution, for example:Example input:
echo <%= @host.name %>
Example rendering:
host.example.com
Example input:
<% server_name = @host.fqdn %> <%= server_name %>
Example rendering:
host.example.com
Note that if you enter an incorrect variable, no output is returned. However, if you try to call a method on an incorrect variable, the following error message returns:
Example input:
<%= @example_incorrect_variable.fqdn -%>
Example rendering:
undefined method `fqdn' for nil:NilClass
- <% -%>, <%= -%>
-
By default, a newline character is inserted after a Ruby block if it is closed at the end of a line:
Example input:
<%= "line1" %> <%= "line2" %>
Example rendering:
line1 line2
To change the default behavior, modify the enclosing mark with
-%>:Example input:
<%= "line1" -%> <%= "line2" %>
Example rendering:
line1line2
This is used to reduce the number of lines, where Ruby syntax permits, in rendered templates. White spaces in ERB tags are ignored.
An example of how this would be used in a report template to remove unnecessary newlines between a FQDN and IP address:
Example input:
<%= @host.fqdn -%> <%= @host.ip -%>
Example rendering:
host.example.com10.10.181.216
- <%# %>
-
Encloses a comment that is ignored during template rendering:
Example input:
<%# A comment %>
This generates no output.
Troubleshooting ERB templates
You can use the Foreman web UI to troubleshoot ERB templates.
The Foreman web UI provides two ways to verify the template rendering for a specific host:
-
Directly in the template editor – when editing a template (under Hosts > Templates > Partition tables, Hosts > Templates > Provisioning Templates, or Hosts > Templates > Job templates), on the Template tab click Preview and select a host from the list. The template then renders in the text field using the selected host’s parameters. Preview failures can help to identify issues in your template.
-
At the host’s details page – select a host at Hosts > All Hosts and click the Templates tab to list templates associated with the host. Select Review from the list next to the selected template to view it’s rendered version.
Generic Foreman-specific macros
You can use Foreman-specific macros in your ERB templates to generate URLs, indent code, and reuse common patterns across templates.
| Name | Description |
|---|---|
indent(n) |
Indents the block of code by n spaces, useful when using a snippet template that is not indented. |
foreman_url(kind) |
Returns the full URL to host-rendered templates of the given kind.
For example, templates of the "provision" type usually reside at |
snippet(name) |
Renders the specified snippet template. Useful for nesting provisioning templates. |
snippets(file) |
Renders the specified snippet found in the Foreman database, attempts to load it from the |
snippet_if_exists(name) |
Renders the specified snippet, skips if no snippet with the specified name is found. |
Template macros reference
You can use macros in ERB templates to add user inputs, load host data, and perform other tasks when writing provisioning, job, or report templates. Availability and options vary by template type.
For more information about the macros available for each template type, navigate to the following pages in the Foreman web UI:
-
Monitor > Reports > Report Templates > Create Template for report templates
-
Hosts > Templates > Job templates > New Job Template for job templates
Click the Help tab on these pages for more details.
- input
-
Using the
inputmacro, you can customize the input data that the template can work with. You can define the input name, type, and the options that are available for users. For report templates, you can only use user inputs. When you define a new input and save the template, you can then reference the input in the ERB syntax of the template body.<%= input('cpus') %>This loads the value from user input
cpus. - load_hosts
-
Using the
load_hostsmacro, you can generate a complete list of hosts.<%- load_hosts().each_record do |host| -%> <%= host.name %>
Use the
load_hostsmacro with theeach_recordmacro to load records in batches of 1000 to reduce memory consumption.If you want to filter the list of hosts for the report, you can add the option
search: input('Example_Host'):<% load_hosts(search: input('Example_Host')).each_record do |host| -%> <%= host.name %> <% end -%>In this example, you first create an input that you then use to refine the search criteria that the
load_hostsmacro retrieves. - report_row
-
Using the
report_rowmacro, you can create a formatted report for ease of analysis. Thereport_rowmacro requires thereport_rendermacro to generate the output.Example input:
<%- load_hosts(search: input('Example_Host')).each_record do |host| -%> <%- report_row( 'Server FQDN': host.name ) -%> <%- end -%> <%= report_render -%>Example rendering:
Server FQDN host1.example.com host2.example.com host3.example.com host4.example.com host5.example.com host6.example.com
You can add extra columns to the report by adding another header. The following example adds IP addresses to the report:
Example input:
<%- load_hosts(search: input('host')).each_record do |host| -%> <%- report_row( 'Server FQDN': host.name, 'IP': host.ip ) -%> <%- end -%> <%= report_render -%>Example rendering:
Server FQDN,IP host1.example.com,10.8.30.228 host2.example.com,10.8.30.227 host3.example.com,10.8.30.226 host4.example.com,10.8.30.225 host5.example.com,10.8.30.224 host6.example.com,10.8.30.223
- report_render
-
This macro is available only for report templates.
Using the
report_rendermacro, you create the output for the report. During the template rendering process, you can select the format that you want for the report. YAML, JSON, HTML, and CSV formats are supported.<%= report_render -%>
- render_template()
-
This macro is available only for job templates.
Using this macro, you can render a specific template. You can also enable and define arguments that you want to pass to the template.
- truthy
-
Using the
truthymacro, you can declare if the value passed is true or false, regardless of whether the value is an integer or boolean or string.This macro helps to avoid confusion when your template contains multiple value types. For example, the boolean value
trueis not the same as the string value"true". With this macro, you can declare how you want the template to interpret the value and avoid confusion.You can use
truthyto declare values as follows:truthy?("true") => true truthy?(1) => true truthy?("false") => false truthy?(0) => false - falsy
-
The falsy macro serves the same purpose as the truthy macro.
Using the
falsymacro, you can declare if the value passed in is true or false, regardless of whether the value is an integer or boolean or string.You can use
falsyto declare values as follows:falsy?("true") => false falsy?(1) => false falsy?("false") => true falsy?(0) => true
Host-specific variables in templates
You can use host-specific variables in templates to access host data such as architecture and operating system.
Note that job templates accept only @host variables.
| Name | Description |
|---|---|
|
The architecture of the host. |
|
Returns an array of all bonded interfaces. See Parsing arrays in templates. |
|
The method of system provisioning, can be either build (for example Kickstart) or image. |
|
The SSL certificate name of the host. |
|
The disk layout of the host. Can be inherited from the operating system. |
|
The domain of the host. |
|
The Puppet environment of the host. |
|
Returns a Ruby hash of facts from Facter. For example to access the 'ipaddress' fact from the output, specify @host.facts['ipaddress']. |
|
Returns the host’s boot loader password. |
|
The host group of the host. |
|
Returns a Ruby hash containing information on host parameters. For example, use host_enc['parameters']['lifecycle_environment'] to get the lifecycle environment of a host. |
|
Returns |
|
Contains an array of all available host interfaces including the primary interface. See Parsing arrays in templates. |
|
Returns array of interfaces with given identifier. You can pass an array of multiple identifiers as an input, for example @host.interfaces_with_identifier(['eth0', 'eth1']). See Parsing arrays in templates. |
|
The IP address of the host. |
|
The location of the host. |
|
The MAC address of the host. |
|
Returns an array of managed interfaces (excluding BMC and bonded interfaces). See Parsing arrays in templates. |
|
The assigned operating system installation medium. |
|
The full name of the host. |
|
The operating system family. |
|
The major version number of the assigned operating system. |
|
The minor version number of the assigned operating system. |
|
The assigned operating system name. |
|
Full path to the kernel and initrd, returns an array. |
|
The URI used for provisioning (path configured in installation media). |
|
Returns the value of the specified host parameter. |
|
Returns |
|
Returns |
|
Returns the primary interface of the host. |
|
The compute resource provider. |
|
Returns the provisioning interface of the host. Returns an interface object. |
|
The partition table name. |
|
The Puppet CA server the host must use. |
|
The OpenVox server the host must use. |
|
Returns |
|
The short name of the host. |
|
The IP address of the BMC interface. |
|
The MAC address of the BMC interface. |
|
The name of the BMC interface. |
|
The subnet of the BMC network. |
|
Returns |
|
The primary DNS server of the host. |
|
The secondary DNS server of the host. |
|
The gateway of the host. |
|
The subnet mask of the host. |
|
Full path to the initrd image associated with this host. Not recommended, as it does not interpolate variables. |
|
Full path to the kernel associated with this host. Not recommended, as it does not interpolate variables, prefer boot_files_uri. |
|
Equals to |
|
Returns |
|
Name of the template being rendered. |
|
Returns a boot loader argument to set the encrypted boot loader password, such as --md5pass=#{@host.grub_pass}. |
|
Returns a string assembled using the port and the baud rate of the host which can be added to a kernel line. For example console=ttyS1,9600. |
|
Returns the root password configured for the system. |
The majority of common Ruby methods can be applied on host-specific variables. For example, to extract the last segment of the host’s IP address, you can use:
<% @host.ip.split('.').last %>
Kickstart-specific variables
You can use Kickstart-specific variables in provisioning templates to inject host data and installation options.
| Name | Description |
|---|---|
@arch |
The host architecture name, same as @host.architecture.name. |
@dynamic |
Returns |
@epel |
A command which will automatically install the correct version of the epel-release RPM. Use in a %post script. |
@mediapath |
The full Kickstart line to provide the URL command. |
@osver |
The operating system major version number, same as @host.operatingsystem.major. |
Conditional statements in ERB
In your templates, you might perform different actions depending on which value exists. To achieve this, you can use conditional statements in your ERB syntax.
In the following example, the ERB syntax searches for a specific host name and returns an output depending on the value it finds:
-
Example input:
<% load_hosts().each_record do |host| -%> <% if @host.name == "host1.example.com" -%> <% result="positive" -%> <% else -%> <% result="negative" -%> <% end -%> <%= result -%>
-
Example rendering:
host1.example.com positive
Parsing arrays in templates
While writing or modifying templates, you might encounter variables that return arrays.
Use Ruby methods to parse arrays so that you can extract parameter values from specific entries, such as interface data from @host.interfaces.
The following procedure is an example that you can use to find the relevant methods to parse arrays in your template. In this example, a report template is used, but the steps are applicable to other templates.
-
To retrieve the NIC of a host, in this example, using the
@host.interfacesvariable returns class values that you can then use to find methods to parse the array.Example input:
<%= @host.interfaces -%>
Example rendering:
<Nic::Base::ActiveRecord_Associations_CollectionProxy:0x00007f734036fbe0>
-
In the Create Template window, click the Help tab and search for the
ActiveRecord_Associations_CollectionProxyandNic::Baseclasses. -
For
ActiveRecord_Associations_CollectionProxy, in the Allowed methods or members column, you can view the following methods to parse the array:[] each find_in_batches first map size to_a
-
For
Nic::Base, in the Allowed methods or members column, you can view the following method to parse the array:alias? attached_devices attached_devices_identifiers attached_to bond_options children_mac_addresses domain fqdn identifier inheriting_mac ip ip6 link mac managed? mode mtu nic_delay physical? primary provision shortname subnet subnet6 tag virtual? vlanid
-
To iterate through an interface array, add the relevant methods to the ERB syntax:
Example input:
<% load_hosts().each_record do |host| -%> <% host.interfaces.each do |iface| -%> iface.alias?: <%= iface.alias? %> iface.attached_to: <%= iface.attached_to %> iface.bond_options: <%= iface.bond_options %> iface.children_mac_addresses: <%= iface.children_mac_addresses %> iface.domain: <%= iface.domain %> iface.fqdn: <%= iface.fqdn %> iface.identifier: <%= iface.identifier %> iface.inheriting_mac: <%= iface.inheriting_mac %> iface.ip: <%= iface.ip %> iface.ip6: <%= iface.ip6 %> iface.link: <%= iface.link %> iface.mac: <%= iface.mac %> iface.managed?: <%= iface.managed? %> iface.mode: <%= iface.mode %> iface.mtu: <%= iface.mtu %> iface.physical?: <%= iface.physical? %> iface.primary: <%= iface.primary %> iface.provision: <%= iface.provision %> iface.shortname: <%= iface.shortname %> iface.subnet: <%= iface.subnet %> iface.subnet6: <%= iface.subnet6 %> iface.tag: <%= iface.tag %> iface.virtual?: <%= iface.virtual? %> iface.vlanid: <%= iface.vlanid %> <%- end -%>
Example rendering:
host1.example.com iface.alias?: false iface.attached_to: iface.bond_options: iface.children_mac_addresses: [] iface.domain: iface.fqdn: host1.example.com iface.identifier: ens192 iface.inheriting_mac: 00:50:56:8d:4c:cf iface.ip: 10.10.181.13 iface.ip6: iface.link: true iface.mac: 00:50:56:8d:4c:cf iface.managed?: true iface.mode: balance-rr iface.mtu: iface.physical?: true iface.primary: true iface.provision: true iface.shortname: host1.example.com iface.subnet: iface.subnet6: iface.tag: iface.virtual?: false iface.vlanid:
Example template snippets
Example template snippets show the correct ERB template syntax and common use cases. You can use these snippets as a starting point when writing your own templates.
The following example checks if the host has the Puppet and Puppetlabs repositories enabled:
<%
pm_set = @host.puppetmaster.empty? ? false : true
puppet_enabled = pm_set || host_param_true?('force-puppet')
puppetlabs_enabled = host_param_true?('enable-puppetlabs-repo')
%>
The following example shows how to capture the minor and major version of the host’s operating system, which can be used for package related decisions:
<% os_major = @host.operatingsystem.major.to_i os_minor = @host.operatingsystem.minor.to_i %> <% if ((os_minor < 2) && (os_major < 14)) -%> ... <% end -%>
The following example imports the subscription_manager_registration snippet to the template and indents it by four spaces:
<%= indent 4 do snippet 'subscription_manager_registration' end %>
The following example imports the kickstart_networking_setup snippet if the host’s subnet has the DHCP boot mode enabled:
<% subnet = @host.subnet %> <% if subnet.respond_to?(:dhcp_boot_mode?) -%> <%= snippet 'kickstart_networking_setup' %> <% end -%>
You can use the host.facts variable to parse values from a host’s facts and custom facts.
In this example luks_stat is a custom fact that you can parse in the same manner as dmi::system::serial_number, which is a host fact:
'Serial': host.facts['dmi::system::serial_number'], 'Encrypted': host.facts['luks_stat'],
In this example, you can customize the Applicable Errata report template to parse for custom information about the kernel version of each host:
<%- report_row(
'Host': host.name,
'Operating System': host.operatingsystem,
'Kernel': host.facts['uname::release'],
'Environment': host.single_lifecycle_environment ? host.single_lifecycle_environment.name : nil,
'Erratum': erratum.errata_id,
'Type': erratum.errata_type,
'Published': erratum.issued,
'Applicable since': erratum.created_at,
'Severity': erratum.severity,
'Packages': erratum.package_names,
'CVEs': erratum.cves,
'Reboot suggested': erratum.reboot_suggested,
) -%>
Appendix C: Job template examples and extensions
You can use these examples to modify, customize, and extend job templates for tasks such as restoring SELinux context, combining templates, or adding power actions.
Customizing job templates
When creating a job template, you can include an existing template in the template editor field. This way you can combine templates, or create more specific templates from the general ones.
The following template combines default templates to install and start the nginx service on clients:
<%= render_template 'Package Action - Script Default', :action => 'install', :package => 'nginx' %>
<%= render_template 'Service Action - Script Default', :action => 'start', :service_name => 'nginx' %>The above template specifies parameter values for the rendered template directly. It is also possible to use the input() method to allow users to define input for the rendered template on job execution. For example, you can use the following syntax:
<%= render_template 'Package Action - Script Default', :action => 'install', :package => input("package") %>With the above template, you have to import the parameter definition from the rendered template. To do so, navigate to the Jobs tab, click Add Foreign Input Set, and select the rendered template from the Target template list. You can import all parameters or specify a comma separated list.
Creating a job template to restore SELinux context
This example shows how to create a template called Run Command - restorecon that restores the default SELinux context for all files in the selected directory on target hosts.
-
In the Foreman web UI, navigate to Hosts > Templates > Job templates.
-
Click New Job Template.
-
Enter Run Command - restorecon in the Name field. Select Default to make the template available to all organizations. Add the following text to the template editor:
restorecon -RvF <%= input("directory") %>The
<%= input("directory") %>string is replaced by a user-defined directory during job invocation. -
On the Job tab, set Job category to
Commands. -
Click Add Input to allow job customization. Enter
directoryto the Name field. The input name must match the value specified in the template editor. -
Click Required so that the command cannot be executed without the user specified parameter.
-
Select User input from the Input type list. Enter a description to be shown during job invocation, for example
Target directory for restorecon. -
Click Submit. For more information, see Executing a restorecon template on multiple hosts.
Rendering a restorecon template
This example shows how to create a template derived from the Run command - restorecon template created in Creating a job template to restore SELinux context.
This template does not require user input on job execution, it will restore the SELinux context in all files under the /home/ directory on target hosts.
-
Create a new template as described in Customizing job templates, and specify the following string in the template editor:
<%= render_template("Run Command - restorecon", :directory => "/home") %>
Executing a restorecon template on multiple hosts
This example shows how to run a job based on the template created in Creating a job template to restore SELinux context on multiple hosts.
The job restores the SELinux context in all files under the /home/ directory.
-
In the Foreman web UI, navigate to Monitor > Jobs and click Run job.
-
Select Commands as Job category and Run Command – restorecon as Job template and click Next.
-
Select the hosts on which you want to run the job. If you do not select any hosts, the job will run on all hosts you can see in the current context.
-
In the directory field, provide a directory, for example
/home, and click Next. -
Optional: To configure advanced settings for the job, fill in the Advanced fields. To learn more about advanced settings, see Advanced settings in the job wizard. When you are done entering the advanced settings or if it is not required, click Next.
-
Schedule time for the job.
-
To execute the job immediately, keep the pre-selected Immediate execution.
-
To execute the job in future time, select Future execution.
-
To execute the job on regular basis, select Recurring execution.
-
-
Optional: If you selected future or recurring execution, select the Query type, otherwise click Next.
-
Static query means that the job executes on the exact list of hosts that you provided.
-
Dynamic query means that the list of hosts is evaluated just before the job is executed. If you entered the list of hosts based on some filter, the results can be different from when you first used that filter.
Click Next after you have selected the query type.
-
-
Optional: If you selected future or recurring execution, provide additional details:
-
For Future execution, enter the Starts at date and time. You also have the option to select the Starts before date and time. If the job cannot start before that time, it will be canceled.
-
For Recurring execution, select the start date and time, frequency, and condition for ending the recurring job. You can choose the recurrence to never end, end at a certain time, or end after a given number of repetitions. You can also add Purpose - a special label for tracking the job. There can only be one active job with a given purpose at a time.
Click Next after you have entered the required information.
-
-
Review job details. You have the option to return to any part of the job wizard and edit the information.
-
Click Submit to schedule the job for execution.
Including power actions in templates
This example shows how to set up a job template for performing power actions, such as reboot. This procedure prevents Foreman from interpreting the disconnect exception upon reboot as an error, and consequently, remote execution of the job works correctly.
-
Create a new template as described in Customizing job templates, and specify the following string in the template editor:
<%= render_template("Power Action - Script Default", :action => "restart") %>
Appendix D: Host parameter hierarchy
You can access host parameters when provisioning hosts.
Hosts inherit their parameters from the following locations, in order of increasing precedence:
| Parameter Level | Set in Foreman web UI |
|---|---|
Globally defined parameters |
Configure > Global parameters |
Organization-level parameters |
Administer > Organizations |
Location-level parameters |
Administer > Locations |
Domain-level parameters |
Infrastructure > Domains |
Subnet-level parameters |
Infrastructure > Subnets |
Operating system-level parameters |
Hosts > Provisioning Setup > Operating Systems |
Host group-level parameters |
Configure > Host Groups |
Host parameters |
Hosts > All Hosts |